I thought I would need to go further back than a month to find five interesting IoT projects. I was wrong. The creativity of all you maker, DIY and project builder types out there continually surprises me. For this week's IoTuesday post, I'd like to share some slick projects that I stumbled upon. Perhaps they'll inspire you to build something, too.
Got any other recent IoT projects or news? Share them in the comments!
Hajime: The Worm That's Securing IoT Devices
Remember the Mirai botnet-based DDoS attack back in October that brought several major sites, including Twitter, to a crawl? The biggest security flaw that allowed Mirai to infect IoT devices (e.g., IP cameras and DVRs) was unsecured telnet ports with default usernames and passwords. Mirai would guess the username and password, implant itself on the device and begin searching for new devices to infect.
While Mirai was used to launch a large-scale denial-of-service attack, a new breed of IoT worm has entered the game. It seems that the worm, named Hajime, is intent on securing your IoT devices. According to Symantec, there is no code in Hajime to launch any sort of attack or denial of service; it just infects your device and closes some ports to make it more resilient to future attacks.
That being said, Hajime does seem to be more robust in that it accepts peer-to-peer commands and not from a single command and control address, which makes the botnet harder to take down. While it would appear the author is a vigilante trying to tackle the ever-growing hurdle of IoT security, will they remain on the side of good in the future? I guess we'll have to wait and see.
Hackaday is following the Hajime development, so I recommend checking there if you want updates.
Non-Invasive Wireless Light Therapy Glasses for Alzheimer's Patients
I can't pass up an opportunity to share projects dealing with assistive technology or electronics used as a potential cure for something so life-altering and pervasive as Alzheimer's disease.
Hackster user Adellar Irankunda created a set of Wireless Light Therapy glasses based on recent research from MIT that shows that specific light patterns (e.g., 40Hz) for extended periods can help increase memory functions in mice afflicted with Alzheimer's disease. The article does point out that what works on mice may not work on humans, so we'll have to see how far this light therapy gets with the FDA.
The glasses use an ESP8266 that allows the flickering light to be controlled over WiFi. In the video, you can see Adellar using a DIY remote control that uses another ESP8266 to access the glasses' interface.
According to Adellar's blurb on Hackster, he's 16, which is incredibly impressive. I know I wasn't making stuff like this at his age.
Amazon Echo-Controlled IR Remote
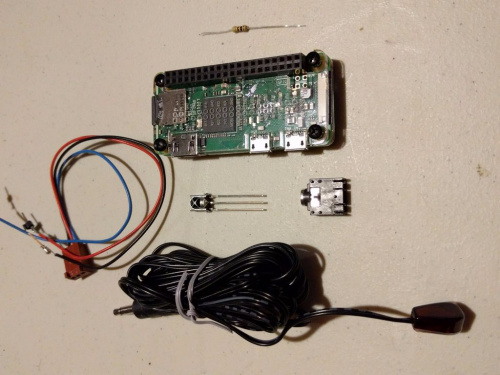
Image by MallocArray
There's probably commercial gear out there already that does something like this, but I know that I've been wanting an infrared-blasting add-on to my Alexa ever since Cortana on my XBox really stopped listening to me.
Well, it's a good thing that MallocArray has created a Raspberry Pi-controlled learning IR remote on Instructables. With a little bit of code, it can respond to Alexa commands, which means I can now change channels and volume (or bedroom fireplace) with my voice. Huzzah.
LoRa Range Testing
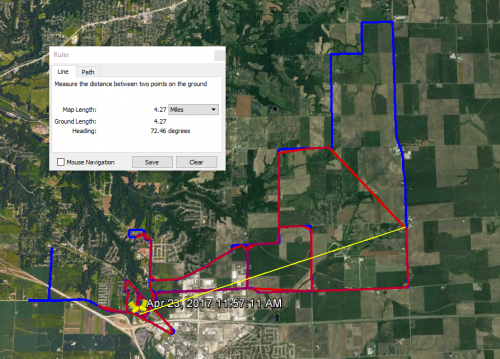
Image by Moser
LoRa (short for "Long Range") is a low-power wireless technology that's gaining popularity in Europe. LoRa operates in the ISM bands (around 865MHz in Europe and the 900MHz band in the United States), and it promises to provide large areas of coverage (miles) with low data rate, which is perfect for things like weather stations and bus signs.
Hackaday shared a post by Moser, who put together a LoRa pager, combined it with a GPS logger and drove around with it. He compared the LoRa GPS remote logging (red line in image above, which corresponds to moments where the LoRa could report its location back to a base station) to his phone's GPS (blue line) and found that the maximum range on the pager was around 4.3 miles. In his words: "Not bad for the pager's 13mm! bad antenna."
Linger
Obligatory Cat Photo by Jasper van Loenen
Another one from Hackaday. In this project, Jasper notes that devices like smartphones are constantly searching for WiFi networks they were previously connected to (unless you disable WiFi). Stores and other third parties could use this information to potentially identify you and track your location (some stores are already doing this with your phone's MAC address).
Jasper's device, lovingly called "Linger," collects all the WiFi requests from everyone around you and then continually rebroadcasts their requests, even when they've left the vicinity. It's a genius "noisy" anti-tracking device, assuming that a store or person is really trying to locate you based on your WiFi requests. You could also just turn off your phone's WiFi, but where's the fun in that?







Connecting to any "free wifi" should be done through a VPN.