
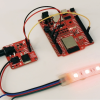
Now for the scary looking picture of the day - grrr! That is an officer of the law holding up a device that was found within a 'PIN pad' in Waterloo, Ontario, Canada. I didn't know what a PIN pad is, so here's a wikipedia article and google images. From the article (November 5th, 2009), it looks like someone has found a couple serial pins on the hand-held credit card reader commonly used within Canadian retail stores. They've wired those pins to a BlueSMiRF. This allows a person sitting ~100 feet away to see all the serial traffic including all the credit card information and pin #s. Not hard - all it takes is a bit of time, and malicious intent. This raises a couple issues...
1) This is going to completely freak my grandparents out. Because they are afraid of getting their money and identity stolen by the hidden thieves of the internet, they refuse to use their credit card on the internet. They are much more comfortable using their credit card at the gas station or grocery store. I've been using my credit card constantly online since 1998 and oddly enough I still possess my identity (it's not worth much). Now my grandparents may never touch a credit card again.
2) All things can be used for good or evil, including our products. You can build amazing things that encourage children to learn (checkout Gever Tulley's amazing presentation at TED), or you can build things that steal. We believe that sharing knowledge and selling products that encourage innovation outweigh the inherent dangers. We believe that stifling innovation or suppressing knowledge lead to much more dangerous outcomes.
And as Christopher says:
I just thought that whether you view this as good or bad publicity, that you should be aware of it.





They could have been cool and twisted the receiver so they could not tell where it came from.... But hey any publicity is good publicity? Now you guys need to find a story where some one saves a school bus full of puppies using Sparkfun gadgets!
Humans hack PIN pads, NOT Bluetooth modules LOL
NOT that I am on the far right but even if some Canadian court tries to make you release info I say - fight the order. Remember the old gun control argument :)
And what is this crap of getting your hands on credit card numbers, what are you going to do with the joke revenue potential from that? Can you buy a million dollar house? Ride the NASDAQ with serious leverage so to be set for life? Not a chance, then is it worth it? May be Canadian jails have special "hacker" cell blocks where they keep out the "lovers" :)
Bau,
It's not about credit card, but rather debit cards.
Canadians prefer to use a debit system off of their bank accounts, rather than pay 20% interest that credit cards offer up here. I'm sure you can see the damage this would cause financially.
I just have to give you guys props for posting this and opening it up to discussion at all.
With most companies, if they found out their products were being used like this, they'd be all "LALALALALA NOT US, WE DIDN'T DO IT, NOBODY SAW US, HA! WE WAVE OUR LAWYER THREATENINGLY IN YOUR DIRECTION!!"
I think by being open about ALL potential uses of your stuff, you build a case against those who might likely knee-jerk against you in a paranoid and misinformed way.
My respect for your company just went up at least another notch or two.
Thanks Jetdillo! It means a lot to hear it from our users.
How do you think firearms manufacturers feel almost every time they look at a newspaper? The toolmaker cannot be held liable for the actions of the tool's user.
I know that this is criminal use of clever technology, but part of me hopes that the hacker used better wire management than what's shown in the picture. This is a sloppy mess. I would be surprised if the signal could be read at 10 feet, much less 100 from all the noise bouncing around. Besides, there are much more legal and profitable ways to use some of the awesome products from Sparkfun. I hope everyone who used the ATM was alerted to this fraud.
Agreed.
Way too complicated. All ya need is 1 bad employee and a dummy reader that looks like the regular one. All it would do is read the card and store the pin..... no need to reverse engineer anything.
"Oh the machine is broke, i can't give you a receipt"
maybe i should clarify... maybe we shouldn't be worried about encrypting everything and trying to be secure, maybe find out why people are inclined to steal stuff to begin with
Did nobody read the entire article but me?
re:pin pad
"If its gone for a matter of time that should spark some interest"
Spark some interest?
Spark?
C'mon, does no one but me find that frickin' hilarious?
or I could have had too much coffee.
that is also a possibility.
Hah! Busted! I'm sure that the Waterloo Record will be hearing from SPARC International's lawyers any moment now. :-)
Gotta admit, if the naming of a product were ever to predispose it to a life of crime, "BlueSMiRF" would definitely be it.
I think it was irresponsible and inappropriate for them to show the Sparkfun logo and URL in that photo, without mention in the article to prevent reader confusion...
The "Bricking" of a device when tampered can be done by using lithium coin cell batteries or ultra capacitors to provide power to static ram devices that hold critical data that the main processor reads to determine if the device has been tampered with or not.
The tamper switches then are wired in series with the battery supply to the static ram device, if tampered with they will loose the data stored in them.
By using a processor with EEPROM capability, it is possible to make the software ignore the tamper test upon initial power up of the device, but require it to do the tamper checks thereafter.
This avoids the catch-22 situation of how to defeat the tamper switches initially.
If the processor has both static ram and EEPROM resources, all of these functions can be built into the same device which makes it more difficult to hack.
However, any system that is left in the hands of a sufficiently skilled person can be cracked given enough time. This just makes it a bit more difficult.
Simple methods that rely on nothing but physical situations are still liable to work best. For example, breakaway connections that destroy connectivity... and look exactly like the pre-broken pins they are mixed in with. Pair that with silicon-etched information about which ones are supposed to be broken, seal that under a tamper-proofing layer, and you've made it exceedingly difficult to manage to get into one without bricking it.
Or, for more fun, take one of the lovely PiN phototransistors (a.k.a. "tiny solar cell") that SparkFun currently sells, and put it somewhere unobtrusive, or a handful of them wired in serial, and set them up to apply a reverse bias voltage to a critical bit of hardware that is, again, under tamper-proofing sealant along with the core chip. Would cost more in time and effort to fix that than it would to simply build a trojan pad from scratch.
Practical? Probably not, but fun to think about.
Simple solution for the keypads: Make the pin pad cases out of clear plastic that way you can clearly see if there is a bunch of extra stuff packed in there.
The only problem is that 90% of the general populous wouldn't know what to look for. You could still put this stuff in there and it would work for almost as long.
Anyway, I don't know about you guys, but I found the picture freaking hilarious. I certainly don't condone doing anything illegal with the products here, but I'm the kind of person that would try to obtain a higher quality image of this, make a huge poster of it and put it on the wall if I worked there.
I'm glad to see that you guys aren't freaking out over this and requiring everyone to sign their life and privacy away to buy a bluetooth chip or similar nonsense. That probably sounds like a backhanded compliment (i.e. "you aren't acting like the gestapo"), but I really mean it. I'm glad you're taking this sensibly.
Waterloo Region....good thing i moved away from there this summer....j/k...not about the moving, but waterloo is pretty nice tho
...and it's not like this is the only device available on the Internet that would have accomplished the same thing. If this were the worst threat we had from consumer-level technology this might even be newsworthy.
As it stands I say hey- free advertising is the best advertising. (Is it me or does the guy in the picture look like he just broke the crime of the century or something?)
One of my tutorial web pages has a statement at the bottom: "Use your knowledge for good; not evil". It was meant as sort of a joke, but the point is valid.
Rob
Doesn't all Bluetooth hardware have an UUID?
If Sparkfun got the ID from the police they could find who ordered that BlueSMiRF.
Each module does have a unique MAC address (not sure if that's UUID). But we eat Bluetooth modules like candy. We don't record what MAC ends up on what product, and we don't record what MAC #s shipped with which individual orders. All we could (maybe) do would be to pin the bad MAC address to a batch of modules we received, to the rough date that our production line soldered that batch to products. Then we could see a rough month or two window of orders, but it doesn't bode well. See my comments above in response to Diego.
Don't ask your grandparents where their credit card goes when they give it to a waiter at a restaurant.
A quick impression of the raised numbers/name and the numbers on the back are all that's needed. I think. Then the crook can use that card online or ever the phone easily.
Gil
The good thing about technology is that it works both ways, I bet that all it takes a SQL query and google maps to narrow the suspect list to, say 20 names...
Do it SF team , catch the bad guy!
Hi Diego - We've got pretty strict customer privacy policies in place that prevent us from releasing any information to anyone. Even if we didn't have said policies, we're actually very against doing such a thing. Sure, we could do some data mining and try to figure out who might be doing bad things, but what if we came up with a couple names and they were wrong? Nothing against any authorities, but I really don't want to start a witch-hunt. It's a tough debate with no clear answer.
This is what a well-written warrant is for. The phrase "Not without a court order or warrant; you'll need to talk to our lawyer" when politely delivered to law enforcement might have a snowball's chance in hell of actually evoking a reasonable response, especially if you're not the droids, er, suspect they're looking for. Helping law enforcement write a warrant that is appropriately narrow helps protect customer privacy while giving the cops the information they're looking for. Everyone but the criminals win.
Hi Nate ,
Play along , I bet it would scare the hell out of the guy =]
I know you guys would never do something like that, it is a terrifying thought pointing the finger at an innocent person.it just makes me mad when someone does these things and gives the community a bad name...
Do you know which newspaper the article is from? I happen to live in Waterloo, Ontario, Canada so this one catches my attention quite a bit!
the clipping comes from the record
Clicking on the picture brings up a PDF of the paper. On the top is says Thursday, November 5, 2009 Waterloo Region Record Local, B2.
Gil
I hope SPARC International lawyer won't use this to prove that Sparkfun is giving a bad image to SPARC International.
and for nagmier comments, the idea of bricking the PIN pad. I was thinking how I would do that if I was designing this. I would start with a swith that is not reachable when you open the casing. Then I thought how could you brick something that is no powered?
Exemple: If you remove the power supply from the device and then remove the back cover thus activating the switch, the microprocessor will be off so he will never know that the swt is activated. The only thing possible would be using a onboard battery.
the other idea that I had, was using a light sensor with the switch. So you will have to open the casing in total darkness to try to avoid my trap + you will need to avoid the swtich.
any idea?
Internal "coin cell" batteries.
I work for a company that manufactures PINPads, Though I do not work in that particular division. I'm also pretty sure our devices have at least 2 physical tamper detection schemes and some "software" detection as well. I'm not 100% on that but the exposure I've had seems to point that way.
Thanks to PCI DSS (www.pcicomplianceguide.org) this type of "cracking" should be going by the wayside soon.
PINpads now are required to have a tamper detection circuit of some kind, If they detect that someone has attempted to open the casing they can "brick" themselves, Essentially requiring a replacement device and no longer functioning for debit transactions.
Hopefully this helps calm your grandparents fears ;)
Unfortunately this would not stop them from slapping a reader on the transmission lines coming out of the device.