The term "hacker" gets used and abused a good deal these days. So much so that those who used to label themselves "hackers" have taken to using other terms to distinguish themselves. Terms like "pentester," "information security specialist," "white hat," etc. are now the common names for those involved in the information security world. The definition of "hacker" has been muddied to include anyone involved in DIY technology, beginners and seasoned veterans alike.
I'm not going to go into the standard diatribe about who is and who is not a hacker, or try to define a taxonomy of the different types of DIY technocrats. That's been done to death. Instead, I'd like to explore how the current DIY electronics world meshes with "traditional" information security (and physical security). Why? Because "hacking" (in the context of breaching the security of information) is fun, and it's a fun way to learn a technology. For example, I'd rather learn what a microprocessor stack is by executing a stack overflow exploit than by being taught the same subject in a classroom lecture. Both are valid ways to learn, but the former is certainly more thrilling. Plus, if one can understand how a piece of technology is vulnerable, one can apply that understanding to make the next iteration of that technology less vulnerable, making it better. What follows are some educational examples of hardware mingling with traditional information security.
Standard Disclaimer: The topics discussed in this post are not meant to encourage any kind of illegal behavior, nor does SparkFun condone any kind of illegal behavior. Hacking embedded electronics can and should be done legally and with the goals of learning, and above all, having fun.
HID Attacks
Image Credit: wikipedia.org
From a hardware standpoint, the computer keyboard is a pretty simple device. It takes user input and translates it into the protocol used by most Human Interface Devices, aptly named "HID." However, from a security standpoint, the keyboard creates a huge vulnerability in the computer system as a whole. It doesn't authenticate, any user has access to it, its protocol is simple and well known, and it can be used to control the entire system. For these reasons it's an obvious attack vector.
The most well known example of a keyboard (HID) attack is a hardware keylogger.
Image Credit: keelog.com
This device is connected inline with the keyboard USB connection, and acts as a man-in-the-middle to intercept keystrokes. It then saves or transmits these keystrokes to an attacker. These devices are simple enough to build, and there are plenty build examples online. An Arduino Uno is capable of acting as a HID keyboard, so it can be made into a keylogger with a bit of specialized programming. All an attacker needs is physical access to a computer to use one, and the faith that the device will not be visually detected by the user.
Another example of an HID attack is a device that acts as an automated keyboard. I made a video about this a while ago, where I programmed an Arduino Uno to automatically open a browser and navigate to a particular web page at the press of a button. If the Arduino can do that, then it can automate any set of keystrokes, to install malware, copy private files, etc. In fact, the hacker Linux distribution BackTrack (now Kali) comes with a set of Arduino sketches written for the Teensy that are specifically designed to install backdoors and copy files from the target computer by acting as an automated keyboard.
Vulnerable By Design
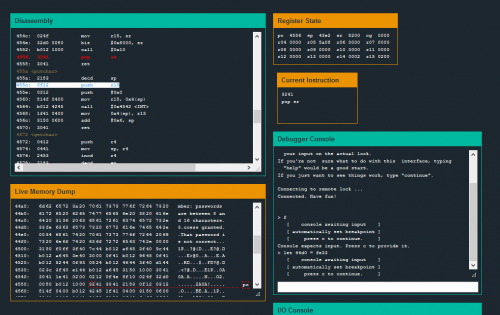
Vulnerable by Design, or "Capture the Flag" games, are pretty common in the infosec world. They are servers or other targets that are built with vulnerabilities in order to teach or practice hacking. My personal favorite is the site overthewire.org, which hosts a series of fun security challenges. Recently, my fellow SparkFunion Nick Poole alerted me to the existence of microcorruption.com, a vulnerable-by-design site where the target is an emulated door lock running on an MSP430 microcontroller.
The objective is to defeat the lock by exploiting an embedded device. The further one advances in the game, the harder the challenges become. This site is a fun way to learn the nitty-gritty of assembly and computer architecture, and, if you already understand those concepts, a great way to understand their vulnerabilities.
Wireless Electronics Hacking
With the popularity of the term "Internet of Things," the security of wireless devices is becoming more of an issue to the general public. Many products are being hastily developed to cash in on IoT's shiny marketing value, and many of these products are developed with no thought given to security.
Wardriving with Zigbee
Image Credit: http://travisgoodspeed.blogspot.com
At first, it may be hard to understand why security is important in this realm. Who cares if my IoT thermostat transmits the temperature of my house in plaintext? In that example, security seems less important. But what if we're talking about your IoT door locks? Your security camera? Your car? The general rule is that if you can access it, a hacker can access it, especially if it has weak or no security. Because the proliferation of IoT is so new, there is not yet a lot of attention paid to security.
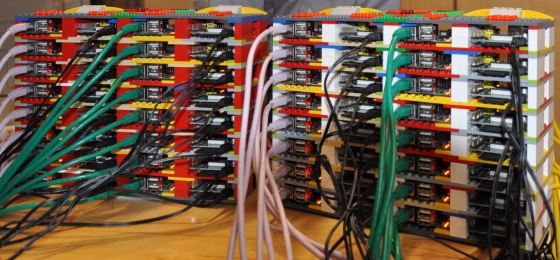
Embedded Linux
The release of the Raspberry Pi created some interesting avenues for hackers. The low price means that a hacker can have access to multiple low power, physical Linux machines without having to spend a lot of money. This makes it perfect for things like modeling a botnet, serving malicious web pages, and distributed password cracking. I personally have used my Raspberry Pi to host a metasploitable system, to mimic a vulnerable computer on my home network.
A Raspberry Pi Distributed Computing Setup
Image Credit: http://liliputing.com
Further Reading
I wish I had the time to go further in depth on the various ways DIY electronics can be relevant in the world of information security, but I think that's a good start for the motivated beginner. I'd also like to go into detail about some of my favorite projects relevant to this subject, but that's another blog post entirely. If you're involved in the security field or just interested in this subject, here are some of my favorite people and projects that are worth taking a look at:
- Josh Datko - creator of the CryptoCape, HOPE and DEFCON presenter
- Travis Goodspeed - another HOPE presenter, with a long resume of interesting hacks
- The NSA Playset - a civilian project to replicate some of the NSA's Prism attack vectors
- MicroCorruption - a capture the flag game for embedded electronics geeks
- Over The Wire - hosts a series of hacking challenges that are great for sharpening your Linux skills








... whistles innocently
Just reading your comment put something on my machine, didn't it.
It was a 2600Hz whistle so I'm stealing your long distance now.
I never wanted a Pi before, but now after seeing it used as a low cost server for "whatever" use I want one. I have an idea for a project that involves creating bogus traffic on the internet to foil some not so secret information collection systems. It would require millions of devices, but could make all the data collected hard to decipher.
Love the article and probably will more so when I have time to read in depth.
Coming at this from a defender perspective, there's a big opportunity to stop forgetting embedded tech.
I've seen embedded systems running OSes years behind on patches or upgrades; vendors actually won't support updated systems. Yes. Really. I've seen it in telecom and other dedicated gear. It's maddening.
Hm, if only I could think of just one example of, oh, I don't know, a major retail breach where an out-of-date operating systems played a major role in stealing millions of credit cards... :]
A perfect example is, I worked for a phone manufacturer. The phones have an SOC that runs Linux with an undocumented ssh service and all of them have the same easy to bruit force root password. The company is a hardware manf and a software manf so they have no security experts. In regards to patching and upgrades , They would only be updated when a new version of the phone system was updated on the main system which would only happen if the customer wanted a new feature or expected a fix. Technician would also have to take the time to force reboot all the phones to get the update which doesn't always happen. The phone is used by fortune 100 companies.
I have seen this in telecom via a cellphone. They kept on putting garbage on my phone that would eat battery life. So I rooted and changed firmware. The phone worked just fine. They never complained that I had changed it. The phone outlasted my service with them and continues to work better than my new phone with a different telecom. I use it a general purpose computing device now. Alarm clock, MP3 player, etc. At least in the cell phone arena they seem to understand why security patching is important.
I have to say that MicroCorruption is a really cool idea. I actually use the MSP430 for projects and it is neat to see the simulated environment they have put together. I've only gone through the tutorial and the first two challenges and... well, its pretty addictive.