As you may or may not have heard by now, the latest driver update from chip manufacturer FTDI is disabling, semi-permanently, counterfeited chips. I'll get more into the technical details later, but I'm going to open with this:
At this time, SparkFun does not believe any of our products to be compromised by this issue.
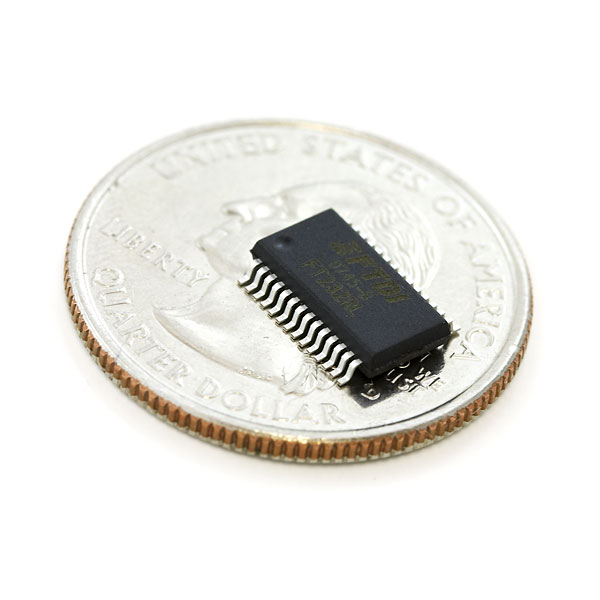
Why does this matter so much? Well, the FTDI USB-to-Serial bridge IC (the FT232, specifically) has been a mainstay of the hardware hacking community for many years. The first USB-based Arduino boards used it; SparkFun's RedBoard still does.
As soon as we heard about it (from Twitter, of course), we immediately began assessing our product line for products which might be of concern. At the moment, we have about 30 individual products using the FT232 chip. We immediately crossed most of them off the list; our in-house assemblies are all produced using chips from reputable suppliers (like Mouser, Digikey, Future, etc.).
We have less visibility into assemblies that come pre-made to us, however, so we immediately set about testing them for vulnerability to this change. Testing is still ongoing, but our preliminary tests show that current stock is not affected. We already had the discussion with suppliers in the past regarding counterfeit chips (you may recall that we had a brush with this issue in the past), so we're quite confident in the product we're currently selling.
If you think something you purchased from SparkFun is affected by this please contact our tech support team immediately. They're really good at what they do, and they'll get your problem sorted out in no time.
Okay, now that we've covered the business end, let's talk nerdy.
From what we've been able to glean from other posts (as yet, we've not been able to duplicate this in house, since we don't have any counterfeit FTDI chips), this is an intentional attempt by FTDI to address the growing population of counterfeit FTDI chips on the world market. With the release of Windows driver version 2.12.0.0 on 26 August, a part of the driver's functionality is to silently change the PID (which is the 16-bit code assigned to a product by its manufacturer to allow the OS to identify the driver which should be used for that part) from 0x6001 to 0x0000.
This change takes place in the target's non-volatile memory, so even after the counterfeit device is removed from the system which altered it, that chip will no longer be recognized as an FTDI-compatible USB to serial bridge, on any computer, under any operating system.
Of course, it may be possible to change the PID back, but any Windows computer with v2.12.0.0 of the driver installed will immediately alter the PID again.
The reason this has become an issue recently (remember, the date on this driver is 26 August) is because the new driver recently hit Windows update. Anyone who's used FTDI chips extensively under Windows has probably experienced the COM port proliferation issue: whenever an FTDI chip is plugged into a USB port that it's not been plugged into before, Windows searches Windows Update for a new driver and assigns a new COM port number to that chip on that USB port. If you don't tell Windows to stop looking online, it will automatically and silently load the new driver which will automatically and silently brick the counterfeit FTDI chips.
I haven't heard anything suggesting Mac or Linux drivers have a similar function, although if they don't now it'll only be a matter of time until they do. It's unclear at this time how the FTDI driver identifies counterfeit chips; until we know more about that process, if you think you may have received counterfeit parts (say, as a part of a knock-off Arduino clone purchased on Ebay at a suspiciously low price), avoiding updating your drivers is probably a wise thing to do.
Keep an eye on this post and the SparkFun (or SFE_Engineering) Twitter accounts; if we find out anything new we'll update this post. I'll be trying to find a non-destructive means for identifying the counterfeits, and if I don't and someone else does, we'll post it here.







No designer can ever be sure that the entire supply chain - yes, including the big, reputable firms - will forever be uncontaminated by knockoffs. FTDI taking this action has made it unsafe to depend on chips with their logo on them - regardless of where you get them.
I can assure the universe at large that henceforth I will no longer use any FTDI parts in any of my designs. I think all responsible designers should follow suit. SparkFun is in a position to make a very powerful statement - not only about irresponsible manufacturers but about open standards generally - by replacing the FTDI cable(s) in its catalog with CDC equivalents.
We'll definitely be having an internal conversation about this, but I can tell you for certain that redesigning all of our products to use non-FTDI parts is completely unfeasible. We've got close to 30 designs using it, and we simply can't pull enough engineers into the redesign process to change all those designs, even if we want to.
I can understand that. And I'm not calling on SparkFun to throw away stock on hand. But when products need to be revised or new products created, I hope SparkFun will remember the dangers involved in trusting FTDI not to pull a Stuxxnet.
Besides, what if the next time they try this little stunt they mess something up and it starts bricking legitimate FTDI product? Maybe a chip revision they missed in driver testing? Who knows what might happen. It's just not worth the risk to use their chips.
Even though you can't be sure whether future production runs of these boards will be dead as soon as you plug them into a Windows machine? That's a huge fallout if you have to bin/rework the whole production series of a board.
While I disagree with the approach FTDI has taken, and agree that going forward it's probably good to avoid FTDI's USB-UART chips (more for technical reasons than ideological), SparkFun doing away with FTDI parts doesn't really make business sense. There's certainly still plenty of products out there - both from SparkFun and other parties - that at least use the FTDI cable interface. Why effectively punish users of those products by denying them a good source of the proper cables?
For now, they are doing the responsible thing to their customers; pointing out that in-house products are not affected (to their knowledge), performing checks of third party widgets, and keeping us posted :)
I’m not saying that SparkFun should stop selling USB-to-Serial products. Surely such products can be procured without using FTDI chips. In fact, by using chips that conform with the CDC standard, they’d wind up supporting an open standard rather than a proprietary one.
Thus the 'going forward' part :)
The "FTDI cable interface" is actually just a bidirectional UART with a particular 0.1" male header pinout. Making an "FTDI cable" with another usb to UART chip that works in all the places an FTDI one works would be trivial.
You won't use FTDI because they stopped "supporting" counterfeit chips (to their knowledge)?If you got a countefeit/reused MCU that claims to be Arduino, and then Arduino pushes out a driver to make it not work, would you stop supporting Atmel/Arduino?
I know the issue is very complex and it's hard to protect your IP/TM and customers who use your products, but why stop using a company's very good product because they pushed out a driver update to brick countefeit chips? Most companies like FTDI do have proper channels you can go through to get their chips. Most of these companies kinda tell you to do this, if not you lose all support from them.
I don't think there's anything Sparkfun can do to help stop counterfeiting beyond reporting to watchdog groups that certain distributors sell fake chips. Changing out all current products that use FTDI with a new one is just unfeasible from a business sense AND open standards. You're basically doing a 180, and that hurts EVERYONE, from those that depend on the products to be FTDI, to those that are potential customers/suppliers. It's better to work with FTDI and the supply chains to try and fix this problem.
The reason to drop FTDI like a hot potato is simple. They are a commodity chipmaker worried about cloning / counterfiting and trying to fight it by attacking the downstream end of their chain. They apparently have a reliable way to detect the clones but instead of publishing it they simply attacked. There is currently no way for an FTDI customer to even know if they or the upstream vendor even used bogus product other than rolling the dice and seeing if product they could have bought a long time ago is going to suddenly die.
Imagine what happens if Sparkfun accidentally got a batch of boards with fakes. The unknown Chinese contract factory won't suffer, the importer won't suffer, SparkFun is going to be left holding the bag and will end up offering exchanges or refunds on products they sold, even stuff sold a year or more ago lest they get dragged into a PR nightmare.
And that is the problem, the risk of using FTDI now rises greatly with the cost of the product it was integrated into. A cheap USB/Serial board isn't bad, imagine the $100 + products they have been built into that might become bricks... and the final retailer is going to be getting the outraged customers and forced into dealing with the fallout.
Yes, I would - because I don't have control over my entire supply chain, and if alternatives exist, switching them is one way to mitigate the risk that counterfeit parts could get substituted, and I get lumped with a bunch of devices that get bricked by FTDI's drivers.
You may have bunch of bricked devices, but you have evidence for the watchdogs to stop counterfeiting. It may be a loss, but have things that can help others.
But it brings up the question of, if your supply chain was bad, why was it chosen to begin with? Most companies like FTDI do mention the distributors they use and their chains, so you are guaranteed a good part.
If you've ever manufactured anything in China, you'll know that nobody there can guarantee 100% that nobody on their supply chain is going to make a bit on the side by swapping some parts out.
And "you've helped the world counterfeiting problem" isn't particularly comforting news when you've just gone out of business. Nor is it a compelling reason not to switch to an alternate part that I can be sure won't suffer from this issue.
This is why you research the supply chain that companies suggest.
With respect to a company going out of business because of counterfeit chips, but how can you stop a counterfeit from happening without providing a trail? Yes it sucks that you lost all this money in a product, but you could help the future by providing this information and data to the watchdogs so they can try and do something, but doing nothing is WORSE. You're letting the counterfeiters win.
The actual choice I face, though, is to pick an FTDI chip and risk this happening - which I'm sure will be educational for everyone, but that's not much comfort - or to pick a competitor's chip, which removes that risk. Why would I take the additional risk of using an FTDI product?
If they did what prolific did a while ago and BSOD/panic on detection, I'd be fine with that.
Deliberate hardware bricking is unacceptable in any context.
Tell that to Apple and other companies that have done it in the past and didn't get any lash back like FTDI is getting right now.
Where does Apple sit in the supply chain? That is the problem here, FTDI is attacking the end users on a supply chain so long the people being hurt have no realistic way to know whether they are buying bootleg product. In many cases the end user doesn't even know who FTDI is or that their product even has a USB to serial conversion chip in it.
That other companies may or may not have done it doesn't make it more acceptable.
Oh, and [citation needed]
So true about not having control of the entire chain. Just look back at what happened to counterfeit airplane parts and Air Force One (http://en.wikipedia.org/wiki/Partnair_Flight_394#Aftermath) (other industry, but the principle is the same)
IEE Spectrum wrote an article on countefeit chips
(oops - replied to wrong post)
I can confirm the following: If you have a counterfeit chip and plug it into windows with the updated driver, your counterfeit chip will be bricked. Once bricked, you can NOT use it on OSX or Linux boxes. However, if you manually install the drivers on Windows, you can use it on that windows box. However, the chip is still bricked. You can un-brick the device with the MProg3.5 Programmer on the FTDi site. Once un-bricked, it will work again on OSX and Linux :) But if you plug it into the Windows box....BRICKED again. For the FTDI boards I have purchased from Sparkfun; these are not affected. Yah!
Update Looks like MS is getting involved. According to this article http://arstechnica.com/information-technology/2014/10/windows-update-drivers-bricking-usb-serial-chips-beloved-of-hardware-hackers/ "Microsoft has given us a statement: Yesterday FTDI removed two driver versions from Windows Update. Our engineering team is engaging with FTDI to prevent these problems with their future driver updates via Windows Update."
Like most of you, I avoid knock-off chips to the best of my ability, but if we aren't able to keep fake pharmaceuticals out of the prescription drug supply chain, then we aren't likely to keep fake chips out of the electronics parts supply chain.
However, to me this is a simple matter of taking illegitimate steps in addressing a legitimate issue. If FTDI wants to have their driver throw an exception when it sees what it believes to be a counterfeit chip, I think that is just fine. No reason they should support knock offs with their driver.
But when they take the law into their own hands, and deliberately do harm to someone's property by bricking the chip, they have crossed the line. I believe that this heavy handed approach will come back to bite them, and they wouldn't want me on the jury if some innocent third party is injured by this puerile behavior.
If they want to take a product using a counterfeit chip out of service LAWFULLY, then there are mechanisms for that. The fact that it may not be practical to apply those mechanisms in many cases does not give license for corporate vigilantism. I'm sure that if any substantive harm comes from this that a judge somewhere will be happy to educate their apparently clueless legal staff on this point.
And what happens if the new driver kills a non-FTDI work alike chip which is not violative of FTDI's intellectual property, or mistakenly kills an oddball production variant of an actual FTDI product?
Just as I stopped buying Sony after they felt free to compromise my computer with a root kit, I will be avoiding FTDI like the plague from here on out.
Anyone who signed off on this concept at FTDI needs to be "bricked" themselves.
The Linux kernel will soon work around the issue and accept bricked devices: http://marc.info/?l=linux-usb&m=141403510729881&w=2
FTDI has now made a statement to reassure customers http://www.ftdichipblog.com/?p=1053
tl;dr - It's not that long, go read it - they do not believe they did anything wrong, per se, but revoked the drivers anyway and will rework them so that counterfeit are still detected but no longer (permanently) modified.
I think this is a poor choice for FTDI. As a board designer, I'll definitely think twice before designing in an FTDI part; not because I think this was heavy-handed (I do) but because if I end up with bogus parts, I could be put out of business. Too bad as - up until now - FTDI have been my first choice. -AR
The correct venue for FTDI's action is in the courts. Bricking a piece of hardware with no indication to the use as to why is completely unethical, as well as potentially illegal. Let's put this in context. A piece of life saving equipment may be stop working unbeknownst to the use and/or tech due to a Windows update. Is that OK ? Is it OK if your mother is connected to it at the time ?
Just as Fluke did with the multimeters, the place to fix this is with the distributors and importers, not with the end user.
If I have a RS232 to USB cable and it stops working, whats to stop me going out and buying another, and it also gets bricked ? How many times will I have to buy one to get a working one ?
This is FTDI's equivalent to th Ford gas tank problem. They figured it was cheaper to pay out at a class action lawsuit in several years, than to pay the legal fees to fight this properly today.
If you read the user agreement or device manuals of these chips as well as the atmels used in the arduino, or windows operating systems, they are not to be used in any situation where it could be a life saving device. If you designed a life saving device with parts not designed for the application or rated for the application, its on you.
You will find that disclaimer on all sorts of parts from all sorts of manufacturers in spite of the fact that they know their parts are routinely used in such settings. It is CYA boilerplate, and since there is frequently no mechanism to ensure that designers have been informed of it, nor a formal licensing process in place for many users of these parts, there is no sure way to know how any particular jurisdiction will view such a disclaimer. In other words, I wouldn't rely on it - especially if I were committing an overt and legally dubious act which was intended to cause a failure. Judges and juries tend to take an uncharitable view of such behaviors.
Actually, they don't attempt to identify the counterfeit chips. They just blindly change the PID exploiting an implementation difference between the real and the cloned chip. The real one will ignore it as invalid, the cloned one will brick itself :(
Really really nasty hack: https://twitter.com/marcan42/status/525202516816842752
To fight chip counterfeiting, some things have to be done drastically. Whether people view it as a good thing or bad, things have to be done to protect product and people.
I can understand the hard stance people in chip manufacturing industry take (I work for a large chip maker too), but there is a risk in taking such hard stance and drastic measures. While punishing the entitty (or entities) stealing the VID/PID and infringing the trademark, such steps primarily punish the consumers and value-add partners. Consumers are not in control of chip choice in this situation. Value-add partners do not have full control either due to complexities of supply chain.
I am sure FTDI put serious thought into this and decided it is worthwhile action. Yet the consumers and value add partners are free to make their own decisions. It is conceivable that a number of value-add partners will decide it is too much of a risk to use products from a chip maker, who tries to protect their market share with such drastic measures. It is also conceivable that consumers will develop mistrust towards the brand - genuine or counterfeit there is not much difference to them.
Long term these defensive measures can easily turn against FTDI because if consumers start avoiding products with FTDI-branded chips in them, value add partners will start turning to other solutions and the precious market share will collapse.
When those "things that have to be done" include destruction of property that doesn't belong to you, then I think you are dangerously wrong.
Counterfeit chips are not "property that doesn't belong to you". This was proven in the Sparkfun multimeter escapades recently. If you violate someones IP, patents or copyright you cannot claim to 'own' the offending products. the fact that the end user is the one sat with a useless chunk of plastic at the end is irrelevant.
Is this a smart move by FTDI? Who knows!!! Probably not. Is it legally sound? Absolutely.
They haven't use legal channel to act, which make it illegal. Do you think that the case of Sparkfun would be the same if Fluke had only took the container and destroyed everything inside themselves? I can tell you, it wouldn't be.
Laws protect us against this, if they believe the device infringed their copyright, it need to go in front of a judge and we have the right to defends yourself.
In this case, though, what is violated is the VID/PID. Is that FTDI's 'IP'? Is using a VID/PID that isn't yours even a legal offense?
( There's also the markings on the case, in most cases - but the software can't see that )
Ah, so the end justifies the means? Nice.
Until a court of law agrees that a product is violative of someone's IP, it isn't proven to be violative, and you are limited as to your options (negotiate, complain loudly, petition the courts for redress).
Until a court of law sanctions a punitive course of action as a remedy for violative conduct, you had best not pursue it, as you are likely to be found liable for any harm that flows from your actions.
Frustrating though it may be, you just don't get to decide for yourself that something is violative, and then apply a remedy of your own choosing.
And this, dear ones, is why Apple and Samsung don't have ninjas assassinating one another's senior management, although they may have both considered that option over a late night round of brandy and cigars. ;^)
As hacks go, it's actually fairly elegant. I disagree with its use, but you have to admire the hack in and of itself :)
It's kind of scary actually. Supposedly, some other models of genuine FTDI chip don't ignore the EEPROM write commands used in the bricking code, so if their driver ever misidentifies one of those as an FT232RL for whatever reason and runs the malicious code it'll quite happily brick those in exactly the same way.
I think that would qualify for a [citation needed] tag :)
Citation: https://twitter.com/marcan42/status/525291106104115201 (I think there are probably other FTDI chips beyond the one named that have this issue, too.)
Here's a photo that shows a visible difference between Genuine and Fake FTDI chips: http://yourduino.com/docs/FTDI-GOOD-FAKE-TerryKing1014.jpg This correlates 100% with those plugged into a machine with "bad" 2.12.0.0 FTDI driver. Fakes are "bricked" (PID set to 0000) the Genuine run fine. This is with a sample of 12 bad and 23 good chips.
I did buy a FTDI breakout board from ebay for 3.5$ shipped. After a month it arrived last week. it worked the first time when i programmed a Pro mini with it. But then 2 days later it stopped working I was puzzled as to what I did wrong. This post gives me a possible answer.
I really don't care if it was really FTDI or not but what I am frustrated about is FTDI company made my item useless!
I suffered the PID change (not in a sparkfun product but a chinese clone) just yesterday when I plugged in a new USB switch. I usually use version 2.08.28 as newer ones always gave me problems (I suppose the "problem" can be detected by new drivers and change PID). I usually take care about that when I plug the FTDI into a new USB port as I know newer versions don't work for me. Yesterday I went to the kitchen just after plugging in and after disconnecting it later it didn't work. I noticed PID was somehow changed to 0000 and didn't know why! I just discovered why happened now reading the article. However, I managed to make it work in windows just editing the files ftdibus.inf and ftdiport.inf in my original 2.08.28 driver folder. I had to make the same change with another Cypress chip I in the pase, so that's why I looked at the PID instantly after the issue. On ftdibus.inf I added a new line to the sections [FtdiHw], [FtdiHw.NTamd64] and [Strings], just copying a valid entry (there are several ones) on them and changing the PID to 0000. On ftdiport.inf, do the same on the same sections. And with that you're done. Driver won't be signed so Windows will show a warning message, but it just works. And as PhillyNJ pointed, using MProg3.5 you can change back PID to 6001. Just did it on my bricked device and it's recognized again with right PID
So I ran an experiment with a Breakout Board for FT232RL USB to Serial:
I used FTDI's FT_Prog utility to reprogram the PID to 0x0000. After unplugging and replugging it in, Windows could not find a driver for it. Bricked.
Then I fired up the Windows Device Manager. After right-clicking on the bricked device, I chose "Update Driver Software" and then "Browse my computer for driver software" and then "Let me pick from a list of device drivers on my computer." I then get a list of device types, and chose "Universal Serial Bus controllers." Choosing "FTDI" as the manufacturer, I saw different FTDI drivers (and possibly driver versions?) to choose from. I chose "USB Serial Converter Version: 2.20.0.0 [1/27/2014]." Then I agreed to a scary-sounding Windows warning.
My computer froze after that (because of the driver install???), but after a restart, the driver was installed, and I used FT_Prog to reset the PID to 0x6001.
Not sure if that would work with a counterfeit chip, and I also don't appear to have the latest FTDI driver installed. But maybe this is an option for unbricking?
Pretty sure that talking my mother through that procedure is a non-starter.
FTDI isn't physically destroying devices, they are preventing counterfeits from being used with their drivers. Drivers that they spent real money on to develop. If you don't agree with their decision, then that's great, you don't have to use their drivers. Contact the manufacturer of the FTDI clone you purchased and get a driver from them. (Because remember, that clone isn't an FTDI device) Don't know who that is? No problem, contact the vendor of the product you purchased. Oh wait, you bought the product for 1/3rd normal price on eBay, shipped directly from China? Well that right there is the hidden cost of buying Chinese knockoffs and clones. No assurance of quality, no support after the sale.
Maybe you did buy from a reputable vendor, but that vendor got screwed over by a supplier and their questionable supply chain. That really sucks for sure. But it's a great example of why FTDI needs to protect their products and their business. Fakes and clones being so prolific doesn't make them ok, it just means that there is a large problem in the industry.
For all intents and purposes, reprogramming the PID to zero bricks the chip. It's not just unusable by their driver, it becomes unusable by ANY driver on any OS. It is recoverable by a guru, but suggesting that this isn't sabotage is disingenuous.
Are the VID and PID values being used by the clones assigned to FTDI? Yes. So the clone manufacturers can pay for a VID, write their own drivers, and assigns their own PIDs. That's after they design their own chip of course. As for PID 0000 being unusable by ANY driver, I see several instances of PID 0000 being used by real devices on this list: http://www.linux-usb.org/usb.ids. Now if we change that statement to PID 0000 for the VID belonging to FTDI being unusable by any official driver, then yes that is correct. Because FTDI controls their VID and can allocate their PIDs as they choose. In this case, they have used 0000 to denote a counterfeit device, which is not supported by their official driver.
If that were true, the driver could just as easily be programmed to not function with the counterfeit, being they were able to detect it...
Absolutely agree with FTDI on this one. The unchecked proliferation of "counterfeit" chips not only hurts their business, but also their reputation for quality. When a poorly designed clone doesn't work as advertised, FTDI gets blamed. It is BECAUSE FTDI takes active measures against counterfeiters that they have a better reputation for quality than any of the others. And that's why I have always preferred their products.
How confident are you that, having done this once, that FTDI won't make a mistake in the future and release a driver that accidentally bricks legitimate FTDI devices?
FTDI's reputation will rest on the quality of their devices and drivers. This is far better than trying to support/fix whatever half baked knock-offs that seek to profit by falsely branding their product as FTDI chips. As I said in my first post, the only way they can assure quality is if they are supporting their own devices. These "other" chip makers are welcome to keep making their chips.. just not under the brand of FTDI. That way, they can develop or lose their own quality controls without blemishing the reputation of a company that has already built a reputation of qualty. Let's look at this another way.. there are two other fairly big makers of serial chips. While their products MIGHT be as good as FTDIs are, I won't use them, simply because there are too many lower-quality knock-offs on the market. Allowing others to impersonate your product reduces your perceived value to that of the worst products that are falsely bearing your brand. Or to put it another way, what is "branding" all about? It's a mark that signifies the maker of any product, for the purpose of being able to discern quality from crap. A brand holder must take reasonable measures to make sure that crap is not bearing their label. otherwise labels, brands, and quality standards are all useless. FTDI is making the right moves to protect their brand. Anything less would be foolish.
Well THIS little incident isn't going to do good things for their reputation, that's certain.
Everyone wants to mention how FTDI did this bad thing and these commentators mention how it could "put them out of business". FTDI is a business too and they are protecting their intellectual property. And lets be frank, most people that have a knock off already had a pretty good idea it wasn't genuine. If its me and my $4 Ebay part bricks--I throw it in the trash. Sounds like Linux users were safe all along and FTDI has now pulled the new drivers. I found this article very interesting, but the comments a bit short sided. That's OK though--everyone can have an opinion.
The huge majority of devices I use have no FTDI on board (Arduino Pro's typically). Although I see that spark fun cannot just change all their devices, if they offered a USB2Serial in 5V and 3.3V that was OS X and Linux compatible and used non-FTDI chips, I'd happily toss my current FTDI adapters (I'll even mail them to FTDI as a demonstration....) and purchase and use that instead. I'm almost included to go buy a couple of clones just to be contrary, but my mom always said two wrongs don't make a right. As tempting it might be.
For most of the Intro to Arduino and Wearable Electronics classes I've taught, installing the drivers (including FTDI) has been the biggest obstruction to getting new students started. Particularly on older Windows machines. I finally started requiring students to bring in their personal computers to ensure they'd have access to help while they install it.
Luckily, however, you can install driver manually. It works then 100% ok even if you don't change PID back.
I have several Genuine and several fake FTDI on Arduino derivative boards. The fakes have laser etched labels that are quite well done. BUT the "Pin 1" dot in the plastic is just a little different. Genuine is large dot, not very shiny Fake is slightly smaller dot and quite shiny You can see this clearly on this photo: http://s.zeptobars.ru/ftdi-FT232RL-real-vs-fake.jpg
Update on FTDI: http://hackaday.com/2014/10/24/ftdi-screws-up-backs-down/
Contains details on how the bricking was done.
I love the fact the FTDI has just announced to the world that their chips can easily be modified and have their firmware changed. If malicious hackers didn't know about it before they do now.
How long until there is malware or ransomware that wipes all ftdi like chips?
Looks like FTDI is pulling the new drivers
http://www.ftdichipblog.com/?p=1053
... oops didn't see Kamiquasi had already posted this
I only want let know that with the same pinouts cypress produce the CY7C65213 ; it probably can replace the ftdi keeping the pcb as is......... I found this on eevblog.
I remember the last scrimmage with counterfeit chips...
I can understand FTDI making their driver incompatible with counterfeit chip, but having that same driver actually make modifications to a chip they did not manufacturer (and without informing, or obtaining consent from the owner of the device) seems quasi legal, at best. If I am effected by this (still investigating), I would think I have a cause for damages for having a rogue driver perform unwanted alterations to my property. IMO, FTDI has really created a mess for itself with this action.
The risks of using knock-off parts is that you don't know what you are getting, but sometimes that's okay. Often performance and reliability is not as good as a genuine part. So knock-offs can't be used in production, but they're fine for hacking purposes. I would prefer to see FTDI publish a "Genuine FTDI Identification Utility" so that I can tell if I've got the genuine part or not. The bricking strategy is far less useful to me and does discourage the use of FTDI parts in new designs.
Just curious, but what if they changed their driver and updated their chip firmware (completely change API for example) with the update? Would everyone still be ticked off? The outcome would still be the same. You would have working FTDI chips and non working counterfeit chips. Also, from how I understand it, the chips are not "bricked." They just don't work with the FTDI drivers anymore (it is FTDI's driver). You could technically write a driver that would work with the counterfeit chips (even with a PID of 0x0000). I think people are overlooking the driver aspect of this. It is FTDI's driver designed to work with FTDI's chips. Personally, I am disappointed that FTDI didn't come up with a sneakier way of detecting and preventing the counterfeit chips from working.
FTDI doesn't own the Linux driver. What they're doing prevents you from using an affected device with Linux.
Anybody remember the whole Fake Atmel sturm-and-drang Sparkfun themselves went through a few years ago ? That to me says that "Avoiding eBay" or "Ensuring you purchase from a reliable vendor" isn't really a solution. You could get fakes from anywhere. This is just a bad, bad move on FTDI's part.
"I’ll be trying to find a non-destructive means for identifying the counterfeits, and if I don’t and someone else does, we’ll post it here."
The test is the exact reverse-engineered chunk of the driver that was posted widely (starting on the eevblog forums). It wouldn't be hard to make that code non-destructive - just write the original value back rather than leaving the zero in place. It's a little dangerous, since you're counting on the second write to undo the damage done by the first, but it's the most reliable test.
This is the patch from FTDI to the linux kernel. https://lkml.org/lkml/2014/10/23/129
It's not from FTDI, it's a joke.
I'm not much of a FOSS purist myself, but it's times like these that really drive home the importance of open source. There's not way in hell code like that will ever get checked into the kernel tree. On a related note, fixing the bricked chips under Linux is significantly easier, since you don't have to workaround Windows' restriction on signed drivers; you just switch to root.
What I'm really interested in is if anyone is going to mount a class action suit against FTDI, since they intentionally damaged the users' property. EULAs don't apply if the drivers are automatically installed, and they can't override statutory provisions (e.g. the EULA would provide them with zero defence in Australia). What would be really interesting though is if someone sued Microsoft for negligence though - that could have some interesting side-effects... (hell, even the bad PR could cause them to lean on FTDI).
Re: Microsoft - In an apparent statement to Ars Technica:
This is a personal first: Kudos to Microsoft for doing the right thing.
I'd love to be the fly on the wall in that conference call between Microsoft and FTDI....
Hmm, I'm not a lawyer (but I'm going to play one in this post), but I can't see a class action lawsuit. Claimant: Dear FTDI, your update bricked my component which I now know to be stolen goods and I want you to compensate me for my loss of stolen goods. FTDI: Please surrender your your stolen goods to the nearest FBI office, alternatively, provide your name, adddress, and a convenient time for arrest for knowingly possessing stolen goods.
I, too, am not a lawyer - however I do know that it would depend on the jurisdiction in question, and what their views on possession of counterfeit goods are.
I stress counterfeit, because you mentioned 'stolen' - which tends to be covered by different laws. For the U.S., for example, the federal law appears to only govern trafficking in counterfeit goods / possession with the intent to sell, and items that are intended for the use of producing items of financial transaction (be it coin blanks, coin stamps, obligations, securities, etc.) where the qualifier 'for sale' does not apply. This may vary state-by-state, and very likely will vary country-by-country. So it may very well be that possession of the item is perfectly legal. Possessing knowingly (or 'could have reasonably known to be') stolen goods, on the other hand, is illegal, but even then under further qualifiers.
What I’m really interested in is if anyone is going to mount a class action suit against FTDI, since they intentionally damaged the users' property
Well said.
I think that patch was intended to be tongue-in-cheek. I can't begin to imagine that it will be merged.
That patch is legit - signed off by the maintainer of that subsystem. They really are that dumb.
I don't see it getting merged, though.
The maintainer of the subsystem works at TI, not FTDI. It's a joke.
This is very interesting article and the comments, some a bit harsh, also have been very interesting. Thanks to everyone for stating facts and their stance. It is very interesting story. Thank you Sparkfun for doing this.