In our 9 year history, we have been extremely lucky with our legal entanglements. We received a Cease and Desists in 2009 and in March, we received our first subpoena. I'm writing today to explain a little bit to folks on the American legal process as seen from a business. I hope this educates a few people about how it works.
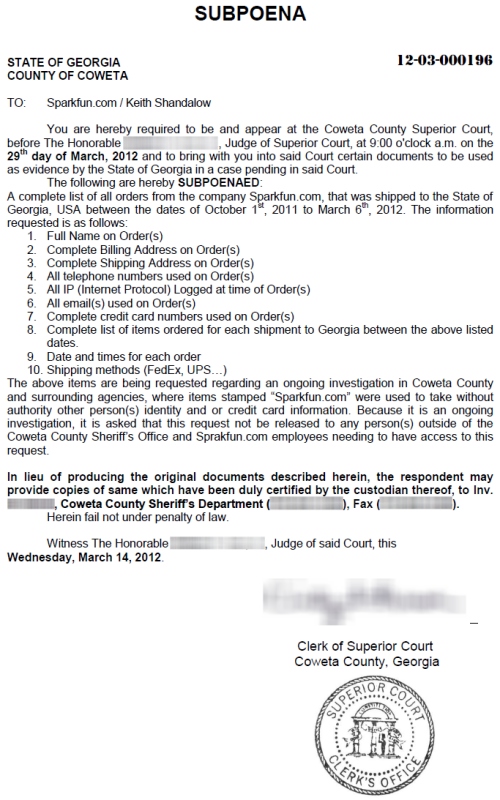
In early March we received some inquiries from a Sheriff's office in a state in the Union. Their office had found credit card skimmers installed in gas pumps along a major highway. One of the PCBs had the SparkFun logo so they gave us a call and started asking for customer information. We respectfully declined letting them know we don't give out customer information to anyone. A few days later we were served a subpoena via email.
I want to be very clear: creating devices that steal credit card numbers are illegal and cause pain for a lot of people. We know our parts can be used for good or for evil. We have zero tolerance for those who use them for evil. I will offer our technical services to any law enforcement that may need help reverse engineering a device. It is obvious the law enforcement agency is requesting this information to put a stop to this activity. However, I also believe strongly in the right to privacy and the protection of personal data.
Needless to say, I have learned a lot about our legal system during this process. A subpoena is public record once the case is closed. We were asked to use discretion when posting full names and to delay our homepage post until the investigation was closed so that we didn't impede the case. To our knowledge no arrests or discoveries were made.
You can say 'no' to a subpoena if you have a very good reason to refuse. We were informed that if you do say no, the law enforcement entity issuing the subpoena will issue a warrant, contact your local sheriff and appear at your work to obtain the requested information. Obviously, this type of escalation would be good for no one.
Please read the subpoena carefully. The request for 'all orders' seemed like they were casting a very wide net without cause. Discussing this issue with our counsel and working with the law enforcement agency, we agreed to obtain the orders that had the product on it, not all orders as required by the subpoena. This ended up being about 20 orders. In my opinion, one order is too much information. While I believe this legal process protects us all from wrong doing, turning over any piece of data goes against every fiber in my being. But without any further legal options, I made the decision to turn over the sub set of data.
I want everyone to know that we take your data and privacy extremely seriously. We guard it with the highest levels of security and confidentiality. If we are legally forced to turn over data, we promise you we will work with the law enforcement agency to do everything in our power to limit the amount of information released.
Please know that subpoenas are very serious, but they are not set in stone. The law enforcement agency was simply trying to do their job and worked with us to limit the scope while getting the information that they needed. I hope you are never served a subpoena but if you are sent one, don't be caught flat footed. Please let this homepage post serve as a reason to raise your hand and ask more questions.





Good thing y'all are employed by SPARKFUN.com and not SPRAKFUN.Com
I think that everybody did the right thing in this instance.
The police were perusing all leads to find out what was going on--and when a logo is stamped on something, it makes sense to go and investigate who was sold that item. If it was a custom made knife that only one place in the city makes then you would expect them to go in there and get the records of who bought that knife. You guys have been copied by China before, sure--even your logo on occasion. But that was clearly your bright red board and logo, and I don't think chinese cloners would go that far...
And SF did good by not just handing out customer data willy-nilly to any badge that happens to ask for it. And then they worked with them to give them only RELEVANT data which I am sure actually helped the investigation by not adding noise into the investigation. After all, all evidence has to be ruled out and by not providing them any evidence that clearly has no chance of even being useful... Big timesaver.
BRAVO ALL AROUND! Lets hope that we can catch the guy, but if not we should move to two-factor authentication for our credit transactions and not just having a card present and knowing the PIN... but maybe having a smart chip on the card with some encryption software run on it as well?
Spokehedz said it perfectly. Thanks, Sparkfun, for protecting my privacy to the RIGHT extent.
Well said. It sounds like reason prevailed here, on all sides.
"Reason will prevail!" _Charlie Kelly, Janitor/Attorney
I appreciate beyond words that you are a company and a group of people that upholds your personal values and look after your customers even after the money has changed hands. That kind of consideration and thoughtfulness is just one of the many reasons I keep coming back :)
If I lived in George, the first thing I would do is get a stop order, or risk my personal info and buying habits becoming part of court/public records.
Thoughts: Given that they have the part, you would think that they would narrow the search to orders with the part on it. The IP address seems like a waste of time given they have CC and addresses. Of course narrowing it to the state is funny in that it assumes criminals respect state lines.
How exactly is this info presented (assuming you don't want to annoy the judge)? Hardcopy? Sorted by ip address? On a flash drive in tab delimited text?
It was very surreal. Just a small csv file emailed to the investigator.
Wait what? They had you email a CSV file with complete billing addresses and credit card numbers. I'm sure that file was encrypted and isn't just sitting on the coweta.ga.us email server waiting for someone to hack it now.
Neither credit card numbers nor IP addresses were included because we don't retain that information for our own protection as an organization.
Which makes me a happy bunny!
Too many companies hoard data they dont really need and notice it when it all blows up in their face.
This whole blog post is an excellent way to show the community your conviction on this and as I said it makes me a happeh bunneh :p
Alright, it's settled. We gotta build a robot to fight crime.
Makes you wonder - if Nate says "We have zero tolerance for those who use them for evil," that's kind of a warning to those who use Sparkfun parts at all for crime. There is a property-law convention called "Reasonable Foreseeability".
Now that Sparkfun has been served with an information request and informed by law enforcement and the courts that their devices are being used by people committing a crime - Sparkfun would be best guided by their council to take a mitigating action for the specific part used in the crime, since it's likely it'll happen more than once more until someone publicly gets caught and bad-guys stop shopping at Sparkfun. These types of actions could be as simple as laser etching a serial number on the board and logging it with each sale. This would reduce further the total amount of data they would have to release (to one purchase). And for you criminals out there who are reading this after building that card skimmer - just think about this:
A serial number can be covered with a white silk-screen (which they already use) so you wouldn't see it unless you scratched all of the silk-screen off - but then, they could also hide it under a large SMT component, or print it visibly under the solder mask. It wouldn't even have to be "numbers and letters" - it could be a 2D barcode, spread out over both sides of the PCB, on the back-side of every resistor, the PCB edge... and it could be laser etch or UV dye, or….
Evil-Doers beware, Sparkfun has your scent and is probably plotting your doom...
As cool as that sounds, what about automated justice when the rules are so poorly written?
I'm very glad that my automobile was not pulled over and cited for riding through downtown Shreveport, LA where it would presumably spook the horses.
Or how about not purchasing a whole chicken on Fridays? How then could we justify our wonderful college football'n'wings weekends?
My concept is wrapped in the basics of batch control - a "grown-up" part of mass producing products. In the chip business we laser etch each chip die, so that we know what wafer and what X/Y location of the wafer it was from - and the date of manufacture, foundry, etc. A 2D Data-Matrix barcode can be etched as small as 100um2 (about 4mills2). It's kind of like the VIN on a car, the batch code on a package of meat etc.
What if someone loaded the pick-and place machine with a tape-reel that contained diodes the manufacturer put in backwards one day (it actually happens). If that got missed in quality control, and a customer found it - they could proactively find any product which used that reel and pull the product off their shelf and get in touch with customers with rework or exchange info.
It has the side effect of helping law enforcement, but only if a good manufacturing and inventory-control procedure is correctly attached to the sales/distribution process.
Laser etching a PCB with a serial number is actually the fastest and easiest way to do it in a production line. You don't have to etch the final serial number on a board until it gets to the pick-and-place stage (installing components on the board), and it can be the final step before the PCB panel is ejected from the pick-and-place machine on the way to soldering. That serial number can reference a database that has the sesrial number for each part (if applicable), or at least each part's tape-reel, tube, or tray batch number.
It's a good process to track all of these things when manufacturing a product that has more than two parts, just for reliability, inventory management, and liability control. I'm not saying that Sparkfun employees are taking parts off the production line for their own use - but with a system that requires input-to-output to be balanced, they could at least prove that.
In the end, releasing 20 people's order information, relatively harmless and useless data, in an attempt to catch a criminal who is likely doing serious damage to thousands of people seems like fair tradeoff.
At first it seemed like the law enforcement was bullying SparkFun to collect data, but they also showed themselves to be reasonable by compromising on the requested data-set.
I think this post sits as a good reminder to your customers, that you shouldn't use SparkFun products for evil, because it could catch up to you in unexpected ways.
They are asking for far more than a small subset of orders.
A list of all orders going to georiga in a six month window.
That's going to be a lot more than 20 people.
Also, this info will probably become public record. Possibly including all of the credit card numbers. That will make for a one stop shop for identity thiefs.
And why do they want the shipping method used?
This request isn't reasonable.
Shipping method seems more reasonable than IP address or credit card. If they can track the package to the shipping provider, they can ask to see who signed for the package.
The best way to get away with something like this would be to design your own board and put something like "ATM security module" on the silk.
Not that any of us would do that, of course :-P
I think that:
you did the right thing with the limited release of pertinent information.
you are a class act by being very transparent in this situation.
Nate,
Sorry, but I've got a bit of a different view on this matter.... Turning over customer data may go "against every fiber in your being", but when the going got tough, you sure folded like a cheap suit....
Subpoenas are tools used by law enforcement to gather data in criminal investigations, but that does not mean that automatic cooperation is required. Law enforcement agencies love to use them because it's easy to intimidate people (how long did it take you to fold?), and it's a low-effort means to do their jobs (it sure beats staking out the gas pump to catch the perp.!) There are, ummm, were plenty of grounds on which you could have objected to the subpoena. Unfortunately, they all take time, effort and money, which I suspect was the basis for your acquiescence, despite your feeble denials to contrary. This was basically a business decision - it was less costly to divulge confidential data then it was to fight for your principals. Imagine how the 20 people (probably all innocent customers!!) feel about having their data shipped off to some nameless/faceless bureaucrat? I'd be pissed!
I'm a libertarian at heart, and when I see (formerly) trusted institutions like Sparkfun giving up personal data for some (perceived) good, it makes my skin crawl......
Bottom line? Sparkfun takes our data and privacy seriously unless and until they get a scary letter asking them to toss aside their (professed) principals! Then? All bets are off!!!
John
Hi John - I hear you and you're right. I don't like how it turned out at all. The way the timing turned out I had to make a decision with little time and incomplete information. I'm a data privacy hawk at heart and it really does pain me to give up anything. If I had to do it all again I would want to get a lot more legal options rather than the recommendations that I was given. I was caught off guard and at the time I made the best decision I could. We will certainly be much better prepared for the next one. I really do want to have this post serve as a piece of education to other folks who get a subpoena in the future.
IMHO they did the right thing - I hate internet censorship and all the SOPA CISPA ACTA and other horrible bits of legislation, but they were downright breaking the law, and deserved to get caught. Plus, SparkFun doesn't support their actions, so would probably have been quite keen to be of some help/ cooperative.
Not true. As far as I understood, none of the 20 people who got their data handed off where breaking the law and they are now in a police database. That said, I think Sparkfun's response was better than the alternative in any conceivable way.
While I wasn't involved with the decision in any way, I do know that we routinely turn down requests for information. Also, I suspect that there's a good chance they would have returned with a warrant. If that were the case, we would have been required to turn over the rather large and scattershot stack of documents indicated in the subpoena rather than the 20 we supplied. Also, please keep in mind that this is likely to have happened to you on several occasions elsewhere without your knowledge, we're doing our best to be transparent and gather criticism (like yours) which will inform our decisions in the future should we ever have to deal with a similar situation.
Let's be honest here - how many other companies do we know that would be as open as this?
What if you encrypted all personal and order information? Maybe they couldn't force you to give them your encryption key. Having a warrant wouldn't do any good for them then.
EDIT: just realized: aren't warrants usually issued to let them search only one building? What if you had one or more server farms with the other always providing encryption keys for the other? That way they take your servers all they like - you just turn revoke access to the keys and they get nothing.
Maybe they need a button to clear order histories.
Sounds like you'll need to find another source of PCBs for your credit card skimmers.
I remember seeing these skimmers on a TV show, like "cops". A policeman removed a device from an ATM and I saw clearly the sparkfun logo and I just thought...oh dear.
Hmm. Shouldn't they have blurred that? That must be breaking some kind of copyright.
No. Copyright law does not apply to logos. Trademark laws do. Trademark laws protect companies from other people making products and selling it as that company. TV does not need to blur out the logo. If they did, the news would never be able to broadcast in public.
Many recorded shows blur out products and logos for a different reason. If, for some reason, that bit of film cast the trademarked company in bad situation, the film company could potentially be sued for defamation. Defamation doesn't really count in reporting shows, since the bad thing actually happened for real, but it could be considered defamation in fictional or set up shows (Mythbusters for example).
The cop show had every right to show the logo. While it doesn't really make Sparkfun look good, one of Sparkfun's products was used in that crime. The show also didn't call attention to the Sparkfun logo (I assume). Also, considering the number of company logos (Visa, Mastercard, Star, Cirrus, etc) on a typical ATM, half the screen would be blurred out :)
I live in Florida and we had similar reports down here (I actually worked in the petroleum industry as a service tech at the time). While I don't like the wide net that was cast by law enforcement in the end working with them and your council seems to have produced the best result with the least amount of damage. The fact that you have been open an honest with us (your current and potential customers) goes a long way as most companies would not disclose this information at all.
Thank you. It's been hard. I'm not satisfied with the outcome but it's one more lesson we've had to go through. Hopefully others can make a more educated decision.
Interesting position to be in. Can I ask whether you independently informed the 20 customers about the release of their information (other than this posting on the home page) ? If I was one of these customers, I would be a little concerned that my information had been released, even if you were legally required to do so.
Also, what about the wording "... it is asked that this request not be released ..." - is "asked" a legally binding requirement, or just a suggestion?
What do you suggest they put in the body of that email, "hey watch out, the cops are on to you"?
Seconded.
Just an FYI...it's "counsel" not "council". Unless you sought legal advice from your municipality, which I wouldn't recommend ;)
-m
Good call - fixed. Thanks!
Turning over any piece of data goes against every fiber in your being? Butchering of that expression aside, that is pretty hyperbolic, don't you think? This isn't warrantless wiretapping, or a SWAT raid of Sparkfun, just a part of an official (and public!) legal investigation.
Did I use it wrong? Sorry - I often misuse sayings.
What I found eye-opening was the simple process in which my name could end up on a list of 'persons of concern'. I never took this class in college so I found it exceptional that a county clerk in a different state, with a simple email template, could compel a business to turn over records. This is my (perhaps poor) attempt at a PSA.
Uh, Nate, Are you saying that sparkfun was never actually properly served the subpoena above? it's my understanding that an email does not constitute proper legal service. Did your counsel advise that email was proper service in this case or did they at least send you smoething in dead tree form via (registered/certified return recipt) postal mail or ups/fedex/etc, or possibly a registered process server? It would not bode well with me if you just handed over the info after getting an email with something that simply looked like a subpoena. While it is good and proper to work with the authorities in cases such as this and Sparkfun is to be commended for limiting the information that was released I would hope that in cases where this comes up Sparkfun would insist that the law and legal process is strictly followed including asking the requesting agency to properly serve you with a subpoena requesting the agreed limited info. in the end, I'd hope you would be polite and courteous with authorities while at the same time insisting they too follow the law. at least I would hope that your counsel got it legally negotiated to where what was agreed upon to finally be provided was agreed upon in writing and signed by a judge of competent jurisdiction. I'd hope that sparkfun in the future would be prepared to ask for a bit more in the future such as requiring subpoenas being properly and legally served, not simply requested via email (make them use a method were they can prove you got it and when that meets all legal requirements of valid service) and that you would be ready in the future with such options as motion to quash for being over broad.
as much as I'd like to see a checkbox in my account pretaining to "store no history" I realize that for business audit and accounting reasons some data pretaining to such records about where sparkfun sourced a product or service from, when, what it was, and where it went along with how it got paid for. that could be buying 0603 resistors from A_vendor with the ultimate "customer" for those items being SparkFunPickNplace01-MPU6050BOBrun03 ;) or that customer XYZ ordered an MPU-6050BOB, that it was paid for and that it was ultimately shipped/delivered ok. these records need to be maintained as just basics of what makes a business run. the difficult decisions are related to the retention policies for this data. those guidelines should follow minimum legal standards as required by statute and where not mandated by statute be limited to that which is necessary for the smooth and competent running of the business. much of those data retention policies should be public and posted on the web. Brennen's comments below are quite apt as related to the business case for data retention. it's good know sparkfun is looking at this.
I will also echo the comments of JohnM. & member 23790 who's comments below on this matter I pretty much agree with and include by reference.
Sparkfun is to be commended for the openness and honesty demonstrated here and their willingness to (seriously) consider customer comment on this matter.
As a Georgia customer, I appreciate your transparency in this situation. I did not make any orders in the affected timeframe, but I still feel better knowing that if my information had left your organization, I'd have known about it.
After the case was closed and you were able to post this information, did you also directly contact the individuals that were directly affected?
Anybody know the item number for the credit card skimming kit? I can't find it in the store...
jk
But seriously, though, does anyone know what the actual part was? I'm guessing something innocuous like a breakout board or power supply or something, but I'm still curious.
It would have to be an item that not many people want to buy, as only about twenty orders contained the item (according to the article).
No, I'm leaning towards a more frequent purchase: It had 20 orders from Georgia between the dates of October 1, 2011 and March 6, 2012.
It included a Sparkfun PCB, so that narrows it down significantly.
My bet is on an Arduino Pro of some kind.
as am i
Check out krebsonsecurity.com for actual pictures of credit card skimmers (did not see any with SF products in it). Pretty sophisticated devices. The fancier versions now send the data via GSM so the crooks don't have to go back to the ATM and risk getting caught.
Always shield the keyboard when entering your PIN!
http://krebsonsecurity.com/all-about-skimmers/
Link for the lazy.
Hmmm, I wonder what one of the original electronics hackers, Benjamin Franklin, would say about this issue? Wait, we don't have to wonder!
Benjamin Franklin: They that can give up essential liberty to obtain a little temporary safety deserve neither safety nor liberty.
This asks for complete credit card numbers, how did you respond to that? Do you have the ability to extract card numbers from logs, your bank or VISA, or is there some sort of storage system involved?
If you are storing things in any way I'm confident that you're doing it in a safe way, but I'd like to hear the details if possible.
Hopefully, with the answer "In accordance with our Merchant agreement with the credit card companies, and to comply with the PCI regulations, we do not store complete credit card numbers on our systems."
Bingo.
So, in other words, "we told them we didn't have the data to meet this subpoena requirement"
That must have been so satisfying to write. basically - screw you, govt.
which makes me wonder how the SONY hacking incedents led to so much CC theft...?
was SONY not following the same rules maybe?
AFAIK, Sony had credit card numbers stored in plaintext in a flatfile. facepalm
how would they even parse something like that in an efficient manner??
storing it like that seems like just asking for trouble (which they got!)
A surprising amount of webshops store credit card information in an insecure manner. It is something everyone should be aware of.
Getting a second card for use online only is a nice line of defense. I have such a thing, and it is linked to a different account in my bank that only holds enough funds for small orders. If I need more I log into my ebank (using two-factor auth) and move fund (free of charge for my bank) to the right account. Fairly easy, and fairly secure.
I got screwed once (by the Warhammer Online system amusingly...) and talked to my bank and they refunded me the money the same day.. even though the warhammer online buggers refused to handle the situation.
It can be a hassle, but security and ease of use usually sit on opposite ends of a scale >.
Another comment mentioned that they did not provide credit card numbers or IP addresses, as SparkFun does not store that information.
Sadly, the direction that law enforcement in this country has taken is one of "Panic first, reason later". This is not new - ask any Japanese-American who was here in the early '40's. But is has increased at an exponential rate in the past decade. Thankfully, some companies, such as Sparkfun, and some people, such as Nate and Sparkfun's council, are willing to question first, and react appropriately. If someone is using a particular Sparkfun product to nefarious ends, it is a waste of time and manpower for law enforcement to have to go through every order of portable phones and huge comedy buttons. And by isolating customer information released to only include orders that include the product found, Sparkfun has done a huge service to its customers, Georgia law enforcement officials, and itself. Thank you, Nate.
Don't most privacy policies have an exception for cooperation with law enforcement? That's certainly my expectation!
http://www.sparkfun.com/static/privacy
Did you point out there there are counterfeit spark fun parts around? Did you point out that a criminal might have purchased it another state?
Dear Microsoft, we found hackers using your Windows OS, please share your customer data for the past 20 years. X(
The Usual Suspects! PIC, AD, ATMEL, TI, BURNS, KEMET... Book'em Dano!
I wonder how likely it is that a person doing credit-card skimming use their own credit card and address to buy the equipment :-)
This reminds me of a quote that I picked up in school somewhere.
Science(or technology) is neither good or evil, nor is it neutral.
The use of devices purchased at sparkfun are made into something in the form of the creator.
You guys are fighting a good fight resisting these preposterous requests for customer information.
Also, isn't sharing account numbers like credit card numbers rather illegal?
You know that these lawyers will suspect ALL of the people that ordered from Sparkfun to be guilty.
Seriously, F*** those guys.
I think you guys got played, the subpoena is totally fake unless served to your hand by another hand attached to a human who works for the sheriff's office or a process server.
Question is who then got the csv file?
SFE didn't just immediately fire off the requested information, there was considerable communication back and forth between law enforcement officials and our legal counsel. This was not a man-in-the-middle attack.
If I use a T-shirt with the Sparkfun logo superior court can require the entirely human genome ?
Dear Honorable Judge, what about people buying Sparkfun products in other stores? (e.g. Watterott in Germany)
I was wondering this, what if the parts used came from a Sparkfun distributor? Anyway I think the Sparkfun staff handled this rather well.
Credit card skimming is going on everywhere. The real problem is the card companies have failed to provide adequate security. They can't hold up against a simple "man in the middle" attack. Card companies know it. They have solutions that will work. They are just slow to change.
Nate,
Considering that I live within 100 miles from Newnan, GA and order from Sparkfun on a regular basis, I think it is a given I would have been one of those customers that you would have been forced to disclose if you had given in to the originally subpoena request. I very much appreciate your handling of the situation the way you did.
It would have been rather easy for you to just quietly fulfill the original request and never say anything about it as this is what Google and Facebook do on a daily basis. Instead, you did the right thing, spent the extra time, and informed us of what you did as soon as you could. I genuinely appreciate this, and is one of many reasons why I am a Sparkfun customer.
Thomas (in Atlanta)
Don't most gas stations and all ATM's have cameras? lmao
Nate, I think you did the right thing. I live in Georgia and hear about skimming devices all the time due to my job. I didn't make any orders in the time frame so I don't think I was on the list. If anything I hope people become more aware of what they are sliding or sticking their credit cards into everyday. People don't put skimming devices just on gas pumps.
All I have to say is: Thank you.
This actually happened to us as well 2-3 years ago, not that we got this paper, but the Swedish police called us since they had a skimming device where there was a bluetooth module from a company we represented, so they found that we were a distributor in Sweden. There was also other parts and I asked if they could e-mail me a photo of the device. They did, turned out that the card reader was connected to a serial bluetooth module so they could sit at a distance and get the info. We sell quite a few of these bluetooth modules to that city, but when I contacted the manufacturer of these bluetooth modules since I saw the serial number on the device at the photo, the manufacturer could tell me it wasn't sold by us (they keep track on serial numbers for warranty issues), instead sold by their US distributor. So there was no more discussions and we were of the hook. And I guess the people who does this is smart as well, not buying parts locally that could easily be tracked, they were. Dumb of them though not to remove such things as brand and serial number, they was not that smart. Not sure if they cought them though.
One problem is that credit card scammers often use previously stolen credit cards and ship things to construction sites and the like (where they hang out to pick the items up after they're delivered), thus leaving no trace of the true identity of whoever ordered the item.
I am unhappy and wish to express my discontent.
At least you sought counsel and refused to flash your entire customer database. Congratulations, that is the least you could do; and still (potentially) maintain many of us as customers. It is absurd that a non-amateur law enforcement officer would think that it is okay to make such a request, but that just goes to show the sorry state of affairs we live in. Yes please, demand/politely request a subpoena/warrant, it's the minimum possible level of effort, and ought to be provided without hesitation or hard feelings. Consider it your receipt in a professional transaction.
Kudos, you did (belatedly) publish the fact that you'd been served, and that you'd complied. Three cheers for having the honesty and courage to do that. You should make it a matter of policy to disclose all such incidents in a timely manner.
What! What? That admission directly contradicts a statement you made only hours prior. Namely "We guard it with the highest levels of security and confidentiality." Is that how it is in Colorado? Because, where I'm from a csv file sent in email (plain text!) is not what I would have had in mind. A single printed sheet or individual printed sheets, via registered mail would have been better for quite a few reasons.
Zero Tolerance? Really? Zero Tolerance is one of those buzzwords that gets social conservatives all riled up and happy; whilst also getting middle-schoolers expelled and arrested on drug charges, for having aspirin in their backpack. I doubt much good will ever come from blindly casting our cognitive abilities aside and instead judging as an open-loop comparator.
It's not that I want to make it easy for people to commit crimes. It is that, left unchecked, dozens, or maybe hundreds of innocent people who were minding their own, would have ended up part of a criminal investigation. Their info probably will exist in files, paper and computer, into the foreseeable future. Do you have control over how Coweta County disposes of old files, computers, etc? Will they be hacked? It's not unheard of. Yes, I do care more about privacy than the (insured) potential losses of some bankers and or ATM operators.
Imagine that.
Please use the critical comments in this thread to stiffen yourself in the future.
Many thanks for responding promptly (to both of you).
And, re: par for the course. All I can say is good grief. Have you had to turn away a lot of punters looking for big IT iron, or were you able to cobble together some kind of Beowulf cum BeagleBoard Database servers.
I just confirmed with those who know that no credit card information was included in the data provided to law enforcement.
Did your counsel motion to quash the subpoena as being overly broad? I think that is very valid legal option.
Thanks for the full disclosure! IANAL, but you mentioned they "served a subpoena via email," but I'm under the impression that a subpoena can only be served in person?
Consider this is not a subpoena for an individual to appear in court (subpoena ad testificandum), this is a subpoena for information (subpoena duces tecum) and is directed at SparkFun as an organization, not to any one individual. I too am not a lawyer, but it is my understanding that the laws vary from state to state and by the type of subpoena being issued.
You did them a favor. They'd be going through a mountain of data instead of just a short list. The investigators are either incompetent (for asking for way more than they need) or they have way too many resources at tax payer expense (and can pay detectives salaries to go through all that needless info). Either way, their manager should get out the pink slips because at least one person needs to be let go.
You guys are a good company, I've always thought that. Thanks for defending us... I just don't want my address and name in public domain... people scan those and spammmmmmmmmm
Note the wording about tipping off: "it is asked that this request not be released..". That's not enforceable wording, and you would not be in violation of the subpoena if you notified the customers that their data were being released. For example, Twitter's policy is to notify users prior to disclosing their information (https://support.twitter.com/articles/41949-guidelines-for-law-enforcement#section5).
We were told it's a very fine line between notification and what might be seen as tipping-off. Thanks for the link to twitter's guidelines. Perhaps we can bake something into our policies and terms of service.
would you be able to release the info on which product they where using?
was is something very specific like a credit card reader, or just something generic like a lipo boost converter to power the project?
also please post the schematics and instructions for installing them in gas pumps, kthx.
I'd like to add my appreciation to that expressed by others. You have to strike a balance between meeting your legal operations and protecting the privacy of your customers, and IMO you went above and beyond by negotiating a reduction in the amount of customer records provided.
Thank you
The subpoena was issued by a state law enforcement agency. They really can't do much if the criminal crossed state lines, though I suspect THIS crime might have drawn the interest of the FBI since it involves banking (and bank robbery is a federal crime). So, I'm a bit surprised that you didn't hear from the g-men on this one. Anyway you guys did the right thing. I hope the Georgia officials learned something in how to conduct such requests in the future and that they destroyed the info on the customers that were not involved in this business.
I do not understand the logic here - just because the crime was committed in a certain state does not mean the criminal was living in that state...
I believe US states have different rules for crimes across state borders, I'd bet they only had authority to investigate inside Georgia, and if they had a reason to believe it was across borders they'd involve higher-ups.
Correct. This was being investigated by the Georgian authorities. Meaning they only have jurisdiction over people/things in their own state. If they wanted to investigate persons across state lines, they would have to make it a federal crime, and get the FBI involved, which may not be possible depending on the type of crime they classified it as.
Fun fact, if you've ever wondered why on a lot of crime drama's they lump all kinds of seemingly unrelated crimes under 'mail fraud', it is because it is an easy way to get a crime elevated to Federal status. Overly simplified, you just need to show that the crime somehow involved the US postal service.
If you start each line with 1. then it makes sense to number them sequentially. If you specifically start the list at 5. Markdown should be smart enough to understand that you really mean 5.
Take it up with Gruber. :)
Thanks. It would be nice it that was mentioned in the formatting help under the comment box. A link in the formatting help to a more detailed guide might also be nice.
Does SparkFun even log IPs?? I don't think you have to by law, and 99.999% of the time it is a waste of HDD space.
yeah, one of my own servers is hitting 500mb/week for accesss.log and i'm down to 300mb free (i'm cheap and dont want to pay for more quota)
Logrotate is spiffy ;)
I am confused. You've now just potentially tipped off the people responsible for this. While I appreciate being told things like this I appreciate it even more if culprits like this are caught. You could have told us 'after' they caught the guys (or gals).
I am also confused as to why they would only ask for shipments going to Georgia. Limiting the purchases of just one state makes no sense. The culprits could easily be out of Florida for example.
It would make more sense to limit it to just the items ordered unless they know something that we don't.
Read the article. He says the case is already closed, and is now public record.
"A subpoena is public record once the case is closed. We were asked to use discretion when posting full names and to delay our homepage post until the investigation was closed so that we didn't impede the case. To our knowledge no arrests or discoveries where made."
"I am also confused as to why they would only ask for shipments going to Georgia."
I'd imagine, since it's the Sherrif's Office, that they only have jurisdiction in Georgia (if not only Coweta county), and if it were someone outside of Georgia that did it, they'd have to escalate it to the FBI or somesuch.
Why is a warrant such a bad thing? Because cops are showing up at your office? Interesting that this comes in time when Twitter just communicated they don't give away anything without a warrant:
http://www.itworld.com/legal/275884/twitter-resists-subpoena-release-users-data-without-warrant
I think it is due to the fact that the warrant may not correctly identify the subset of data needed and law enforcement could cause an outage of all IT infrastructure if the specified evidence was a full server, set of servers, etc. In the end the law is entitled to the identified evidence. I think it was wise that Sparkfun was proactive, limited to scope of what was originally requested and worked with law enforcement. It is a bummer that their product was used in a way to purposefully harm others though.
I have heard of cases where Law Enforcement pepes turn up with warrant thinking that it is fine to put Hot Swap HDDs in evidence bags - If they did that, they would definitely need a SWAT team to deal with IT.
Reminds me a bit of this story from a year or so ago--- http://www.pcmag.com/article2/0,2817,2387447,00.asp
I know. It makes me feel pretty awful. It may sound like an excuse but we don't exactly have the legal support twitter poses.
Well, presumably the warrant would be issued for the data in the initial request - every order. Not just the 20 that was given.
It's much harder to get a warrant. Police can issue a subpoena with very little basis, but to get a warrant you need to convince a judge that you have probably cause.
Credit card skimming is 'scary' and usually leads to quick warrants.
Oh sure, that's probably true. But we don't know what would have happened, so there is always the risk. The law is an ass, after all.
admit it's a very different situation. twitter gets a request for a specific person. Also dubious to request for people only taking part in political activity and not crimes.
Yeah, and Tweets are Intelectual property whilst orders are logged commercial events
I love Sprakfun.com
Who knew that there were so many lawyers on SF?!
Wow. I just learned about this. I must say that I'm disappointed that you caved so easily. This was a subpoena, not a warrant - you didn't have to comply and you certainly didn't have to hand over the personal information of 20 customers who you nor the authorities had any proof of wrongdoing.
I understand the position you were in but I also think that you should have stood up for your customers more.
This is a sad day.
I just gained a whole new level of respect for SparkFun. They've always been quick to ship and respond to dumb emails, but to have the fortitude to DO THE RIGHT THING in the face of a pretty intimidating subpoena goes above and beyond. I can only imagine that any other company (even those that �do no evil�) would have immediately caved to the full demands of law enforcement, without a thought for customer privacy / constitutional rights, and surely wouldn't have even imagined making the request public.
You guys (in the sense that includes both genders, like 'ustedes') rock.
I'm not sure that "respect" is the word I'd use to describe my feelings for a company that willingly handed over personal data of 20 random customers when they didn't have to.
I like the system we have: we all give up a little privacy (and occasionally our time and attention) to help catch people who rip other people off.
There would be far less of this nonsense if everyone with an education had an adequate paying job with benefits. The schools that charge so much for tuition should also assume responsibility of ensuring first out-the-chute jobs for their customers (students -graduated or not) as opposed to the gamble games students are forced into today.
Desperation has the unique ability to cause normally good people to do that which they must to survive...give a kid a nice expensive education and no job opportunity and, most importantly, a GINORMOUS tuition bill with the FED mercilessly backing it up...and there you have a disastrous concoction...engineered and enforced by the 1% -the highly educated.
For us techno-types there is always the 'dark side' of the force to choose...some go on to design weapons to kill the enemy, while others choose to design medical sensors -or flashing blingies for clothing.
I dunno if it is better to have the desperate ones robbing a bank using a mask, note or gunpoint, or to have them cleverly dupe their victims out of the 'payload' remotely. They gotta eat too. I'm not defending or approving, just pointing out the human condition upon us today. Either way, it is a festering problem. k
Did you at least inform the 20 people whose data you divulged?
Also is there some request process to remove all my information from your systems?
DOUBLE KUDOS for not retaining credit card information!
Kudos to you for being able to work with the law enforcement agency to limit the information disclosore. My primary concern is not for tagging of inventors, but rather, for disclosing their private information. The less my credit card is disclosed to third parties, the better I feel. I've always thought that storing cc information is very bad thing for any dba. It will bite you in the end.
This isn't what I meant when I said "Show me your subpoenas."
LONG LIVE SPRAKFUN!
It sounds like what we call in EMEA a "Belgium virus": Someone is stealing credit card numbers, please help us to catch him by sending all the credit card numbers you may know. Thanks for your cooperation.
this is the misuse of technology
They want complete credit card numbers? We obviously don't have a very intelligent legal system, as retaining "complete credit card numbers" is a violation of federal law, under the PCI-DSS rules.... Unbelievable!
I was just about to erase sparkfun from my list of suppliers , but then got down far enough into the comments to see you DIDN'T give them cc card #'s.
My only question now is, if they check out all these people and they all alibi out, are they going to get the idea that they could have been bought assembled by someone either in Georgia or passing thru Georgia from someone who makes them elsewhere using sparkfun parts? What are they going to do then?
dont give these hateful bastards anything to work with. when they produce a FEDERAL WARRENT then you might concider it until then jurisdiction prevails.
SPRAKFUN.Com ?!
First just because some people are skimming with part purchased from spark fun too bad. the only way you should even think of answering this is if they subpeona the wire and solder manufacturers other wise i would say this is prejudical.
so what.
respond ... well next time we find our selves in georgia then we might stop by and see what going on.
if there are any microcenter stores then ignore it all.
and until they put down the fishing pole and begin to employ some real detective work like reviewing the video of the WaWa, then they can kiss your sweet rocky mtn ass.
in other words ...
What exactly was this "device" with the sparkfun.com logo on it?
I'm a tad late to the comment party, but I'd just like to say that I appreciate how you guys (SF) handled this. As a resident of the state of Georgia, I got a bit touchy when I first read this. I - like most others - value my privacy, and don't appreciate it when mass subpoenas are issued.
Two things I really appreciated about how you guys handled this. 1) You notified the public as soon as you were legally able to 2) You negotiated the subpoena to where only orders involved with the product were released
I have no idea if my information was released, but it would be great (if legally possible) if you could let the people involved know.
Anyway - thumbs up!
To be clear - I mean after the case is closed - if you could notify the people involved. Obviously it wouldn't really work out well for the investigators if you were to notify them if the case isn't closed aye?
Also I wonder how many "scam-subpoenas" exist. What kind of verification methods exist to verify that a subpoena is real?
edit
Just curious: you would be cool with your name, address, IP address, and credit card number(s) being collected by law enforcement agencies during an investigation. This without having any idea whatsoever about whether they knew how to protect that data from somehow leaking out on the Internet or ending up in other completely unrelated investigations?
edit
I am not a lawyer, but it is my belief that you complied with a valid but non-compulsive legal request. It was certainly proper for the state of Georgia to request that you bring certain documents to their court. The fact that your business is in another state leads me to think that you are not compelled to do anything, unless you have retail outlets in that state, or travel to it.
Nonetheless, I applaud your handling of the situation on two points, firstly being reasonable to your customer privacy as well as the scope of what was delivered, secondly the open discussion of your interactions.
Once again, Sparkfun demonstrates it is a fine company indeed.
I'm surprised by the vehemence and "every fiber of my being". I'm sure you send the state and federal government all the details about your employees, their income, SSN, number of deductions, addresses, dependents, age, gender, etc. You give details to OSHA and any regulatory agency. You are always giving out way more private information than the subpoena asked for.
As for customers, what do you put on Customs forms? You tell Customs in the US and the destination country exactly what they bought, their address, and how to reach them. Not that I don't think LE and prosecutors are very heavy handed today, but why is this any different from your automatic revealing of purchases to Customs? It seems you are mixing ideas about information and Internet privacy with commerce in physical goods. Better think this through a little more.
The difference is this is all done with consent. Employees consent to have their income, SSN, etc. given to the government, its part of having a job in this country. If we want our board certified by regulatory agencies we choose to give them some information, but that is information on us as a company not our customers private information. Even customs are something the customer agrees to, maybe not consciously, but agreeing to have something shipped via a reputable shipping company (not a guy shoving parts down his pants and sneaking into the country), means abiding by your countries import laws.
Are you claiming doctor-patient privilege :-) What does your contract with your gateway say in all those pages of small print? It was good to whittle them down to the info that might matter. On the other hand, Nate's attitude is the complete opposite of the original hackers. They felt that all information belongs to everyone - really wide open source.
A potential subpoena is something every customer agrees to, maybe not consciously. Did it ship my USPS? Interstate Commerce? There are so many possible jurisdictions they can pull out that tangling with them is a waste of time and can get very expensive very quickly. Wait till they find some Sparkfun part in a pipe bomb and you get Homeland Security, BATF, FBI, Marshals, and Secret Service in your lobby! I'd go heavy on the preemptive legal advice if I had as many customers as you. There must be some boiler plate everybody uses who sells phones and RF and RC stuff.
I'll bet the case was closed because none of the orders matched their criteria. Looking at this logically, the sheriff's department divulged there were multiple skimmers. They were probably looking for an order with a high quantity of said board and there were none. It would probably be relatively easy for many of your customers to cobble something together to pull info off a card and transmit it via bluetooth to a logger. But one look out on hackaday, instructables, etc., there are very few homebrewed devices that look professional enough to seem legit to a reasonable person. That would probably require a custom made injection molded enclosure. Which implies a design team, software, hardware, ee. Then there's the use of the extracted data and laundering of the money skimmed. Another team to deploy and possibly retrieve said devices without being obvious on a security camera. Seems like you'd need a whole "organization" to pull that off... Just saying.
Which to me makes it seem unlikely to have been purchased in Coweta County. More likely it's national or international and the FBI or Interpol should be looking for someone who purchased many dozen or hundred boards.
I liked that you guys took the time to explain the situation to us, thanks guys!
Coweta County used a rather common approach. Send out a broad subpoena as this will get the recieving parties attention and not just wind up in the trash. They need your cooperation and they were very willing to work with you to get just the information they needed. The subpoena was to let you know that someone thinks that this is serious business. You talked to counsel, contacted them and they got the information they needed without causing too much disruption.
And you posted this which might just act as a deterant to others who might want to get stuff from you to use for illegal purposes.
I definitely believe that no one can predict what can be done in the other tip of the chain. I sincerely appreciate what you do for your customers since they have no write to demand such things.
Yet another reason to do business with SparkFun - Integrity! Thanks guys!
Should move to quash the subpoena. There is no need to compromise when the scope of the subpoena is overreaching, as this one appears to be. Moreover, it is certainly permissible to object to the subpoena and file the motion to quash without responding to it.
Can SFE and others just NOT SELL mag stripe readers? Would that kill the company?
Most likely was a breakout board or a bluetooth modem as the card readers aren't made by sparkfun and don't have sparkfun logos on them. Bluetooth modems from sparkfun have been found in card swipers before, theres a clip from a newspaper somewhere on the site with a picture of one.
that was my guess. OK in the future when making skimmers, hand phasers in the 60 watt or greater range, and quad copter ICBMz, please have the presence of mind to scratch out the logo.
the card readers are also massive compared to most skimmers, would need to be heavily dis-assembled, or just gutted for a read head and nothing else
and read-heads could be taken from a tape deck for much less money and paper trail
Odd that they asked for all orders from Georgia, when they obviously know what part it was that was ordered. They could narrow it down quickly by sending you a picture of it -you only carry 2 mag card readers.
That step would probably narrow down the suspects pretty quickly - excluding the book & blinkie buyers, etc.
Also it could be that the perps could use a shipping address in some other (nearby) state to avoid this. They might actually have a business building skimmers and selling them without being directly involved in placement, and could be selling in multiple states.
Oh well. Good luck with all this. A friend of mine lost his entire company trying to stand up to some silly lawyers who didnt know what they wanted - and got the court to agree to hand over all the company,,, except the data. Duh.
So...I guess it is not technically possible to order a part to another state and transport it to GA? Yeah, I know we are not dealing with rocket surgeons here, but the criminals probably aren't very bright either.
Surrendering customer databases is pretty common. You think amazon & digikey don't do it all the time? The feds are going to trace the serial numbers on every chip, from birth to death.
The question I would have asked the prosecutor before surrendering any information is this: Are all the other manufacturers of components found in this device also getting a summons? That is, if Energizer batteries were found inside, did Eveready have to cough up a list of all the people in Georgia that purchased batteries? If not, then why are Sparkfun components singled out as the root cause of evil.
Wayne
Sparkfun products are largely purchased from a single central location -- this website, which records the information of its customers, making it an easy location to start the investigation. Batteries can be bought anywhere, and don't require any kind of purchaser registration. Ditto most other components, which aren't uniquely marked and can be bought from many locations.
Yeah, you totally missed my point. You can buy Sparkfun products, such as breakout boards with the Flame logo (the kind of products implicated in this) from other online retailers, such as Pololu.com, too. You can also buy them on eBay. I'm sure this device wasn't built solely out of Sparkfun parts, so the issue of who was asked to divulge customer info and who was not is still important.
My concern here is that DIY-related sellers and purchasers will be singled out as "troublemakers" much like the guy who got raided for having a chemistry set at home (http://blog.makezine.com/2008/08/11/home-science-under-attack/). So, the point needs to be made just because we build gadgets at home that does not make us "obvious" suspects in a crime.
there is a lot of comments here, I did not read them all.
What says that the item was not bought from your distributor!?!?
Bravo to SFE, but the truth is, the information requested is probably not relevant in any way. If you're the type to be committing crime, it's in your best interest to not get caught. I'm not here to give anyone ideas, but if I were the customer interested in breaking the law, it would be very easy to defeat this information request by simply thinking outside the box for a moment.
If it were me served with the subpoena, I would have assisted by simply reverse engineering the device rather than giving up customer information. That action would do a lot more to catch the people involved than it would if the customer data were made available per the original request.
Well, I have a comment, also.
I sympathize with your call. It seems like you made the best call you could given the information you had. And I laud your apparently libertarian leanings.
BUT....and this is a biggie....
What if you get subpoenaed to give out a list of all the folk who you have sent an IMU to? By, say, Homeland Security? IMU's are pretty potentially dangerous things, 'specially coupled with GPS.
This is a rhetorical question, but it deserves a bit of cogitation.
I'm sure if you guys were a billion dollar company you would've of dragged them through court and made them limit their request too one persons order. Not quite their yet though, that said I think it's great what you did do and I'm appreciate your efforts. Thank you. It's a shame that some people always ruin the fun for everyone else.
That is a sad thing that people are doing things like that thinking that they will get ahead in life. The only thing that I would use a card reader/writer system for, is for home security.
Thus SprakFun.
I do hope this means that 20 people aren't going to have SWAT teams kicking down their doors at 2am and terrorizing their families. The upside of "all orders in the state over the month" would likely prevent that, but since there are only 20, are they going to bother doing any further investigation before kicking down doors?
Do you feel you have any responsibility to warn those who ordered from you that they might be getting no-knock at the door in the middle of the night and might want to get a lawyer and review their rights under the 4th amendment?
A SWAT response a la "Hackers" would be not only vastly inappropriate but blatantly wasteful. If the Coweta County authorities behave this way, the suspects in question will have humanitarian legal counsel lining up to represent them.
Also, the investigation is now closed and we were not informed of any law enforcement shenanigans.
Another thank you for taking our privacy seriously. Thanks for all of the effort put into working out a solution resulting in the least damage rather than allowing this thing to result in the issuance of a non-negotiable warrant, which would have surely resulted in a much larger release of data.
Thanks for the privacy-no thanks Coweta County, GA (where I went to highschool) for your pathetic inconsiderate nature. If I ever want to see a cow-eat-a schoolbus, I know where to go.
So you're saying you have the motive and the means... interesting. (Big ;)
Actually, I'm saying thanks to Sparkfun for maintaining privacy for those they could. I've got in-laws (good ones) in Coweta and no reason to mess it up at all. lol
It's hard to say that everyone in this forum doesn't have the means, isn't it Mike? ;)
Sounds like I'm singing with the chorus but here's another thank you for your attempts to limit the release of private information.
Thank you for posting your data breech by those under color of authority. Most companies would blindly do what it says and not tell anyone. It's really good to hear Sparkfun really DOES care about it's customers.
I'm always amazed at evil techies who are smart enough to hack complex systems, and dumb enough to leave footprints sufficient to get caught. But I hope you guys at Sparkfun are discussing this with legal counsel, and not thinking you can thumb your noses at the law. You could be implicated as an accessory unless you cooperate. When a person breaks the law, he/she pretty much surrenders rights to privacy. The Supreme Court recently ruled that anyone arrested can be strip-searched -- so much for privacy.
According to the article, they didn't get caught.
I appreciate you protecting our information but realize that since you are located in Colorado you are not subject to the jurisdiction of the Georgia Court so they can't force you to give them information anyway.
That's not entirely true. By themselves they lack the authority, but they can go through the process to get an out of state subpoena.
They could go through a process to get a Colorado judge to issue a subpoena but they didn't because SparkFun gave up the fight without forcing them to do so. There are also other numerous grounds for fighting this subpoena but, again, SparkFun didn't really fight those issues either. A good lawyer would have fought this subpoena if his client was willing to pay to fight it but obviously SparkFun chose to save money and give in. Either way, a Georgia court, by itself, has zero authority in Colorado. At a minimum, they should have forced Georgia to get a proper Colorado subpoena.
Yes, inter-state cooperation between law enforcement increased quite a bit in the last half of the 20th century. Although not too much farther back, around 70 years ago, crossing a state border was almost as much a problem for local law enforcement as going into another country.
Everything I know about inter-jurisdictional law enforcement I learned from "Dukes of Hazzard" reruns.
I'm happy I moved out of Georgia (AND COWETA COUNTY) in July. My information could have been on that list.
Nate et. al., I will never forget the stance you made on 18Jan2012. Revealing this subpoena, and making sure that they only got the information they needed, really holds true to that. I appreciate everything that you all stand for. Thank you for your integrity and committment to the customer. You are one of the few businesses with a backbone.
Thank you spark fun for helping out the Law Enforcement Organization. You provided information that hopefully will catch the bad guys. There should not be any feelings other than pride on your part.
I certainly hope the data turned over helps the authorities, but what really gets me worried is the false positives. In other words there are people on that list (potentially and probably all of them) that are perfectly innocent. I fear having the spot light turned on myself for no legitimate reason and I have similar concern for those on the list.
Hey Nate - But the false positives are just a part of the investigative process. They will use their databases to see if any of the people on the list have priors or are known for something and narrow it down. It is not as if they will break down the doors of every person on that list.
No different then looking at a faulty circuit, sometimes you unsolder the wrong resistor trying to troubleshoot.
I agree most folks on the list won't be bothered but that type of argument ties too closely to 'if you have nothing to be worried about, don't be worried'. I am law abiding. And regardless if I was cleared from a similar list, I don't like being placed on such list.
You raise good points and I don't think we'll clear up this debate any time soon.
I greatly appreciate your high prioritization of personal privacy. Thank you!
That said, I would be OK if my information was part of the set you handed to the police. I can understand being one of the false positives if there was sufficient reason to put me there:
The width of that cast net is important, and it sounds like you worked with the police to narrow it to a completely reasonable and defensible subset of customers. I don't think anyone (including you) should demand more of you than that.
I must admit that I am personally responsible for the execution of many innocent semiconductor devices. I only did it in the name of expediency, well, I killed quite a few in blind experimentation as well, and; I confess, I've done it just to see them die. Nevertheless, I (hypocritically) would like a bit more consideration given to my person than I often afford to the poor innocent components I have needlessly condemned. Call me an elitist if you must, but; I consider myself more important than most electronic devices.
Is SparkFun legally required to retain customer information for an unlimited period of time? If not, it seems like the easiest way to avoid such situations is to delete personally identifiable information as soon as it is no longer needed for business purposes.
Personally, I like being able to go look at my order history that Sparkfun keeps associated with my account.
That's probably the best solution. Retain data for account holders for whom shopping convenience outweighs the privacy risk, and have anonymous ordering for anyone else. When making a one-time order from a website, I really appreciate being able to buy without creating an account. Fewer logins and passwords to manage.
what would happen if the user actually deletes his account though, then there is no logical reason to keep things (beyond legal ones)
may need to legally keep records for x years, just so he cant order&self-delete?
This is kind of a gray area. We don't currently have a delete-your-account feature, although we do disable accounts and scrub the data associated directly with them on request.
I think we're probably always going to keep some record of a given order. We may wind up defining a policy and site features whereby users are able to say "delete as much of what you know about me as is reasonable", and explicitly delineate the set of things which will be retained.
A lot of this just really hasn't come up until recently; there's a whole set of conversations we'll be having internally.
I love order histories, and I personally do not care that much if my order history is released to law enforcement in a limited fashion like the 20-odd orders in this case. The fact that you take the time to discuss it and are aware of the issues is pretty much all the reassurance I need to know it is being handled better than most other websites I shop at..